
mcp-gateway-registry
Enterprise-ready MCP Gateway & Registry that centralizes AI development tools with secure OAuth authentication, dynamic tool discovery, and unified access for both autonomous AI agents and AI coding assistants. Transform scattered MCP server chaos into governed, auditable tool access with Keycloak/Entra integration.
Stars: 426
The MCP Gateway & Registry is a unified, enterprise-ready platform that centralizes access to both MCP Servers and AI Agents using the Model Context Protocol (MCP). It serves as a Unified MCP Server Gateway, MCP Servers Registry, and Agent Registry & A2A Communication Hub. The platform integrates with external registries, providing a single control plane for tool access, agent orchestration, and communication patterns. It transforms the chaos of managing individual MCP server configurations into an organized approach with secure, governed access to curated servers and registered agents. The platform supports dynamic tool discovery, autonomous agent communication, and unified policies for server and agent access.
README:

Unified Agent & MCP Server Registry – Enterprise-Ready Gateway for AI Development Tools
🚀 Get Running Now | Production Deployment | Quick Start | Documentation | Enterprise Features | Community
Demo Videos: ⭐ MCP Registry CLI Demo | Full End-to-End Functionality | OAuth 3-Legged Authentication | Dynamic Tool Discovery | Agent Skills
The MCP Gateway & Registry is a unified, enterprise-ready platform that centralizes access to both MCP Servers and AI Agents using the Model Context Protocol (MCP). It serves three core functions:
- Unified MCP Server Gateway – Centralized access point for multiple MCP servers
- MCP Servers Registry – Register, discover, and manage access to MCP servers with unified governance
- Agent Registry & A2A Communication Hub – Agent registration, discovery, governance, and direct agent-to-agent communication through the A2A (Agent-to-Agent) Protocol
The platform integrates with external registries such as Anthropic's MCP Registry (and more to come), providing a single control plane for both tool access, agent orchestration, and agent-to-agent communication patterns.
Why unified? Instead of managing hundreds of individual MCP server configurations, agent connections, and separate governance systems across your development teams, this platform provides secure, governed access to curated MCP servers and registered agents through a single, unified control plane.
Transform this chaos:
❌ AI agents require separate connections to each MCP server
❌ Each developer configures VS Code, Cursor, Claude Code individually
❌ Developers must install and manage MCP servers locally
❌ No standard authentication flow for enterprise tools
❌ Scattered API keys and credentials across tools
❌ No visibility into what tools teams are using
❌ Security risks from unmanaged tool sprawl
❌ No dynamic tool discovery for autonomous agents
❌ No curated tool catalog for multi-tenant environments
❌ A2A provides agent cards but no way for agents to discover other agents
❌ Maintaining separate MCP server and agent registries is a non-starter for governance
❌ Impossible to maintain unified policies across server and agent access
Into this organized approach:
✅ AI agents connect to one gateway, access multiple MCP servers
✅ Single configuration point for VS Code, Cursor, Claude Code
✅ Central IT manages cloud-hosted MCP infrastructure via streamable HTTP
✅ Developers use standard OAuth 2LO/3LO flows for enterprise MCP servers
✅ Centralized credential management with secure vault integration
✅ Complete visibility and audit trail for all tool usage
✅ Enterprise-grade security with governed tool access
✅ Dynamic tool discovery and invocation for autonomous workflows
✅ Registry provides discoverable, curated MCP servers for multi-tenant use
✅ Agents can discover and communicate with other agents through unified Agent Registry
✅ Single control plane for both MCP servers and agent governance
✅ Unified policies and audit trails for both server and agent access
┌─────────────────────────────────────┐ ┌──────────────────────────────────────────────────────┐
│ BEFORE: Chaos │ │ AFTER: MCP Gateway & Registry │
├─────────────────────────────────────┤ ├──────────────────────────────────────────────────────┤
│ │ │ │
│ Developer 1 ──┬──► MCP Server A │ │ Developer 1 ──┐ ┌─ MCP Server A │
│ ├──► MCP Server B │ │ │ ├─ MCP Server B │
│ └──► MCP Server C │ │ Developer 2 ──┼──► MCP Gateway │ │
│ │ │ │ & Registry ───┼─ MCP Server C │
│ Developer 2 ──┬──► MCP Server A │ ──► │ AI Agent 1 ───┘ │ │ │
│ ├──► MCP Server D │ │ │ ├─ AI Agent 1 │
│ └──► MCP Server E │ │ AI Agent 2 ──────────────┤ ├─ AI Agent 2 │
│ │ │ │ │ │
│ AI Agent 1 ───┬──► MCP Server B │ │ AI Agent 3 ──────────────┘ └─ AI Agent 3 │
│ ├──► MCP Server C │ │ │
│ └──► MCP Server F │ │ Single Connection Point │
│ │ │ │
│ ❌ Multiple connections per user │ │ ✅ One gateway for all │
│ ❌ No centralized control │ │ ✅ Unified server & agent access │
│ ❌ Credential sprawl │ │ ✅ Unified governance & audit trails │
└─────────────────────────────────────┘ └──────────────────────────────────────────────────────┘
Note on Agent-to-Agent Communication: AI Agents discover other AI Agents through the unified Agent Registry and communicate with them directly (peer-to-peer) without routing through the MCP Gateway. The Registry handles discovery, authentication, and access control, while agents maintain direct connections for efficient, low-latency communication.
This platform serves as a comprehensive, unified registry supporting:
- ✅ MCP Server Registration & Discovery – Register, discover, and manage access to MCP servers
- ✅ AI Agent Registration & Discovery – Register agents and enable them to discover other agents
- ✅ Agent-to-Agent (A2A) Communication – Direct agent-to-agent communication patterns using the A2A protocol
- ✅ Multi-Protocol Support – Support for various agent communication protocols and patterns
- ✅ Unified Governance – Single policy and access control system for both agents and servers
- ✅ Cross-Protocol Agent Discovery – Agents can discover each other regardless of implementation
- ✅ Integrated External Registries – Connect with Anthropic's MCP Registry and other external sources
- ✅ Agent Cards & Metadata – Rich metadata for agent capabilities, skills, and authentication schemes
Key distinction: Unlike separate point solutions, this unified registry eliminates the need to maintain separate MCP server and agent systems, providing a single control plane for agent orchestration, MCP server access, and agent-to-agent communication.
Watch how MCP Servers, A2A Agents, and External Registries work together for dynamic tool discovery:
https://github.com/user-attachments/assets/f539f784-17f5-4658-99b3-d664bd5cecaa
Interactive terminal interface for chatting with AI models and discovering MCP tools in natural language. Talk to the registry using a Claude Code-like conversational interface with real-time token status, cost tracking, and AI model selection.
Quick Start: registry --url https://mcpgateway.ddns.net | Full Guide
-
📚 Agent Skills Registry - Register, discover, and manage reusable instruction sets (SKILL.md files) that enhance AI coding assistants with specialized workflows. Skills are hosted on GitHub, GitLab, or Bitbucket and registered in the MCP Gateway Registry for discovery and access control. Features include YAML frontmatter parsing for metadata extraction, health monitoring with URL accessibility checks, visibility controls (public/private/group), star ratings, semantic search integration, tool dependency validation, and a rich UI with SKILL.md content modals. Security includes SSRF protection with redirect validation. Agent Skills Guide | Architecture
-
📋 Compliance Audit Logging - Comprehensive audit logging for security monitoring and compliance. Captures all Registry API and MCP Gateway access events with user identity, operation details, and timing. Features include automatic credential masking (tokens, cookies, passwords are never logged), TTL-based log retention (default 7 days, configurable), admin-only audit viewer UI with filtering and export (JSONL/CSV), and non-blocking async design. Supports SOC 2 and GDPR requirements with who/what/when/where/outcome tracking. Audit Logging Guide
-
🌐 Peer-to-Peer Registry Federation - Connect multiple MCP Gateway Registry instances for bidirectional server and agent synchronization. Central IT teams can aggregate visibility across Line of Business registries, or LOBs can inherit shared tools from a central hub. Features include configurable sync modes (all, whitelist, tag filter), scheduled and on-demand sync, static token authentication for IdP-agnostic deployments, Fernet-encrypted credential storage, generation-based orphan detection, and path namespacing to prevent collisions. Synced items are read-only and display their source registry. A VS Code-style Settings UI provides peer management, sync triggering, and status monitoring. Architecture Design | Operational Guide
-
🔑 Static Token Auth for Registry API - Access Registry API endpoints (
/api/*,/v0.1/*) using a static API key instead of IdP-based JWT validation. Designed for trusted network environments, CI/CD pipelines, and CLI tooling where configuring a full identity provider may not be practical. MCP Gateway endpoints continue to require full IdP authentication. Includes startup validation that disables the feature if no token is configured. Static Token Auth Guide -
🔀 MCP Server Version Routing - Run multiple versions of the same MCP server simultaneously behind a single gateway endpoint. Register new versions as inactive, test them with the
X-MCP-Server-Versionheader, then promote to active with a single API call or UI click. Features include instant rollback, version pinning for clients, deprecation lifecycle with sunset dates, automatic nginx map-based O(1) routing, cascade deletion of all versions, and post-swap health checks. The dashboard displays both the admin-controlled routing version and the MCP server-reported software version independently. Only the active version appears in search results and health checks. Design Document | Operations Guide -
👥 Multi-Provider IAM with Harmonized API - Full Identity and Access Management support for both Keycloak and Microsoft Entra ID. The registry API provides a unified experience for user and group management regardless of which IdP you use. Human users can log in via the UI and generate self-signed JWT tokens (with the same permissions as their session) for CLI tools and AI coding assistants. Service accounts (M2M) enable AI agent identity with OAuth2 Client Credentials flow. Fine-grained access control through scopes defines exactly which MCP servers, methods, tools, and agents each user can access. Authentication Design | IdP Provider Architecture | Scopes Management | Entra ID Setup
-
🏷️ Custom Metadata for Servers & Agents - Add rich custom metadata to MCP servers and agents for organization, compliance, and integration tracking. Metadata is fully searchable via semantic search, enabling queries like "team:data-platform", "PCI-DSS compliant", or "owner:[email protected]". Use cases include team ownership, compliance tracking (PCI-DSS, HIPAA), cost center allocation, deployment regions, JIRA tickets, and custom tags. Backward compatible with existing registrations. Metadata Usage Guide
-
🔎 Enhanced Hybrid Search - Improved semantic search combining vector similarity with tokenized keyword matching for servers, tools, and agents. Explicit name references now boost relevance scores, ensuring exact matches appear first. Hybrid Search Architecture
-
🛡️ Security Scan Results in UI - Security scan results are now displayed directly on Server and Agent cards with color-coded shield icons (gray/green/red). Click the shield icon to view detailed scan results and trigger rescans from the UI. Security Scanner Documentation
-
🧪 Comprehensive Test Suite & Updated LLM Documentation - Full pytest test suite with 701+ passing tests (unit, integration, E2E) running automatically on all PRs via GitHub Actions. 35% minimum coverage (targeting 80%), ~30 second execution with 8 parallel workers. Updated llms.txt provides comprehensive documentation for LLM coding assistants covering storage backend migration (file → DocumentDB/MongoDB), repository patterns, AWS ECS deployment, Microsoft Entra ID integration, dual security scanning, federation architecture, rating system, testing standards, and critical code organization antipatterns. Testing Guide | docs/llms.txt
-
📊 DocumentDB & MongoDB CE Storage Backend - Production-grade distributed storage with MongoDB-compatible backends. DocumentDB provides native HNSW vector search for sub-100ms semantic queries in production deployments, while MongoDB Community Edition 8.2 enables full-featured local development with replica sets. Both backends use the same repository abstraction layer with automatic collection management, optimized indexes, and application-level vector search for MongoDB CE. Switch between MongoDB CE (local testing) and DocumentDB (production) with a single environment variable. Note: File-based storage is deprecated and will be removed in a future release. MongoDB CE is recommended for local development. Configuration Guide | Storage Architecture
-
🔒 A2A Agent Security Scanning - Integrated security scanning for A2A agents using Cisco AI Defense A2A Scanner. Automatic security scans during agent registration with YARA pattern matching, A2A specification validation, and heuristic threat detection. Features include automatic tagging of unsafe agents, configurable blocking policies, and detailed scan reports with API endpoints for viewing results and triggering rescans.
-
🔧 Registry Management API - New programmatic API for managing servers, groups, and users. Python client (
api/registry_client.py) with type-safe interfaces, RESTful HTTP endpoints (/api/management/*), and comprehensive error handling. Replaces shell scripts with modern API approach while maintaining backward compatibility. API Documentation | Service Management Guide -
⭐ Server & Agent Rating System - Rate and review agents with an interactive 5-star rating widget. Users can submit ratings via the UI or CLI, view aggregate ratings with individual rating details, and update their existing ratings. Features include a rotating buffer (max 100 ratings per agent), one rating per user, float average calculations, and full OpenAPI documentation. Enables community-driven agent quality assessment and discovery.
-
🧠 Flexible Embeddings Support - Choose from three embedding provider options for semantic search: local sentence-transformers, OpenAI, or any LiteLLM-supported provider including Amazon Bedrock Titan, Cohere, and 100+ other models. Switch providers with simple configuration changes. Embeddings Guide
-
☁️ AWS ECS Production Deployment - Production-ready deployment on Amazon ECS Fargate with multi-AZ architecture, Application Load Balancer with HTTPS, auto-scaling, CloudWatch monitoring, and NAT Gateway high availability. Complete Terraform configuration for deploying the entire stack. ECS Deployment Guide
-
📦 Flexible Deployment Modes - Three deployment options to match your requirements: (1) CloudFront Only for quick setup without custom domains, (2) Custom Domain with Route53/ACM for branded URLs, or (3) CloudFront + Custom Domain for production with CDN benefits. Deployment Modes Guide
-
🔗 Federated Registry - MCP Gateway registry now supports federation of servers and agents from other registries. Federation Guide
-
🔗 Agent-to-Agent (A2A) Protocol Support - Agents can now register, discover, and communicate with other agents through a secure, centralized registry. Enable autonomous agent ecosystems with Keycloak-based access control and fine-grained permissions. A2A Guide
-
🏢 Microsoft Entra ID Integration - Enterprise SSO with Microsoft Entra ID (Azure AD) authentication. Group-based access control, conditional access policies, and seamless integration with existing Microsoft 365 environments. Entra ID Setup Guide
-
🤖 Agentic CLI for MCP Registry - Talk to the Registry in natural language using a Claude Code-like interface. Discover tools, ask questions, and execute MCP commands conversationally. Learn more
-
🔒 MCP Server Security Scanning - Integrated vulnerability scanning with Cisco AI Defense MCP Scanner. Automatic security scans during server registration, periodic registry-wide scans with detailed markdown reports, and automatic disabling of servers with security issues.
-
📥 Import Servers from Anthropic MCP Registry - Import curated MCP servers from Anthropic's registry with a single command. Import Guide
-
🔌 Anthropic MCP Registry REST API Compatibility - Full compatibility with Anthropic's MCP Registry REST API specification. API Documentation
-
🔎 Unified Semantic Search for Servers, Tools & Agents - Natural-language search across every MCP server, its tools, and registered A2A agents using
POST /api/search/semantic. Works from the dashboard UI (session cookie auth) or programmatically with JWT Bearer tokens, returning relevance-scored matches per entity type in a single response. -
🚀 Pre-built Images - Deploy instantly with pre-built Docker images. Get Started | macOS Guide
-
🔐 Keycloak Integration - Enterprise authentication with AI agent audit trails and group-based authorization. Learn more
-
📊 Real-Time Metrics & Observability - Grafana dashboards with SQLite and OpenTelemetry integration. Observability Guide
-
⚡ Amazon Bedrock AgentCore Integration - AgentCore Gateway support with dual authentication. Integration Guide
The registry includes two example A2A agents that demonstrate how both human developers and autonomous AI agents can discover, register, and use agents through the unified Agent Registry. Agents can programmatically discover other agents via semantic search and use them through the A2A protocol, enabling dynamic agent composition and autonomous agent orchestration.
| Agent | Path | Skills |
|---|---|---|
| Travel Assistant Agent | /travel-assistant-agent |
Flight search, pricing checks, recommendations, trip planning |
| Flight Booking Agent | /flight-booking-agent |
Availability checks, flight reservations, payments, reservation management |
View in Registry UI: Open the registry and navigate to the A2A Agents tab to browse registered agents with their full metadata, capabilities, and skills.
Search via CLI: Developers can search for agents by natural language description:
# Search for agents that can help book a trip
cli/agent_mgmt.sh search "need an agent to book a trip"Example Output:
Found 4 agent(s) matching 'need an agent to book a trip':
--------------------------------------------------------------------------------------------------------------
Agent Name | Path | Score
--------------------------------------------------------------------------------------------------------------
Travel Assistant Agent | /travel-assistant-agent | 0.8610
Flight Booking Agent | /flight-booking-agent | 1.2134
--------------------------------------------------------------------------------------------------------------
The registry provides a semantic search API that agents can use as a tool to discover other A2A agents at runtime. This API enables dynamic agent composition where agents find collaborators based on capabilities rather than hardcoded references.
Discovery API Endpoint:
POST /api/agents/discover/semantic?query=<natural-language-query>&max_results=5
Authorization: Bearer <jwt-token>
Response includes:
- Agent name, description, and endpoint URL
- Agent card metadata with skills and capabilities
- Relevance score for ranking matches
- Trust level and visibility settings
How agents use it:
- An agent calls the registry's semantic search API with a natural language query (e.g., "agent that can book flights")
- The registry returns matching agents with their endpoint URLs and full agent card metadata
- The agent uses the agent card to understand capabilities and invokes the discovered agent via A2A protocol
Example - Travel Assistant discovering and invoking Flight Booking Agent:
User: "I need to book a flight from NYC to LA"
Travel Assistant:
1. Calls registry API: POST /api/agents/discover/semantic?query="book flights"
2. Registry returns Flight Booking Agent with endpoint URL and agent card
3. Uses agent card to understand capabilities, then sends A2A message to Flight Booking Agent
4. Returns booking confirmation to user
This pattern enables agents to dynamically extend their capabilities by discovering specialized agents for tasks they cannot handle directly.
Agent Cards: View the agent card metadata at agents/a2a/test/ to see the complete agent definitions including skills, protocols, and capabilities.
For complete agent deployment and testing documentation, see agents/a2a/README.md.
Provide both autonomous AI agents and human developers with secure access to approved tools through AI coding assistants (VS Code, Cursor, Claude Code) while maintaining IT oversight and compliance.
Centralized authentication, fine-grained permissions, and comprehensive audit trails for SOX/GDPR compliance pathways across both human and AI agent access patterns.
AI agents can autonomously discover and execute specialized tools beyond their initial capabilities using intelligent semantic search, while developers get guided tool discovery through their coding assistants.
Single gateway supporting both autonomous AI agents (machine-to-machine) and AI coding assistants (human-guided) with consistent authentication and tool access patterns.
The MCP Gateway & Registry provides a unified platform for both autonomous AI agents and AI coding assistants to access enterprise-curated tools through a centralized gateway with comprehensive authentication and governance.
flowchart TB
subgraph Human_Users["Human Users"]
User1["Human User 1"]
User2["Human User 2"]
UserN["Human User N"]
end
subgraph AI_Agents["AI Agents"]
Agent1["AI Agent 1"]
Agent2["AI Agent 2"]
Agent3["AI Agent 3"]
AgentN["AI Agent N"]
end
subgraph EC2_Gateway["<b>MCP Gateway & Registry</b> (Amazon EC2 Instance)"]
subgraph NGINX["NGINX Reverse Proxy"]
RP["Reverse Proxy Router"]
end
subgraph AuthRegistry["Authentication & Registry Services"]
AuthServer["Auth Server<br/>(Dual Auth)"]
Registry["Registry<br/>Web UI"]
RegistryMCP["Registry<br/>MCP Server"]
end
subgraph LocalMCPServers["Local MCP Servers"]
MCP_Local1["MCP Server 1"]
MCP_Local2["MCP Server 2"]
end
end
%% Identity Provider
IdP[Identity Provider<br/>Keycloak/Cognito]
subgraph EKS_Cluster["Amazon EKS/EC2 Cluster"]
MCP_EKS1["MCP Server 3"]
MCP_EKS2["MCP Server 4"]
end
subgraph APIGW_Lambda["Amazon API Gateway + AWS Lambda"]
API_GW["Amazon API Gateway"]
Lambda1["AWS Lambda Function 1"]
Lambda2["AWS Lambda Function 2"]
end
subgraph External_Systems["External Data Sources & APIs"]
DB1[(Database 1)]
DB2[(Database 2)]
API1["External API 1"]
API2["External API 2"]
API3["External API 3"]
end
%% Connections from Human Users
User1 -->|Web Browser<br>Authentication| IdP
User2 -->|Web Browser<br>Authentication| IdP
UserN -->|Web Browser<br>Authentication| IdP
User1 -->|Web Browser<br>HTTPS| Registry
User2 -->|Web Browser<br>HTTPS| Registry
UserN -->|Web Browser<br>HTTPS| Registry
%% Connections from Agents to Gateway
Agent1 -->|MCP Protocol<br>SSE with Auth| RP
Agent2 -->|MCP Protocol<br>SSE with Auth| RP
Agent3 -->|MCP Protocol<br>Streamable HTTP with Auth| RP
AgentN -->|MCP Protocol<br>Streamable HTTP with Auth| RP
%% Auth flow connections
RP -->|Auth validation| AuthServer
AuthServer -.->|Validate credentials| IdP
Registry -.->|User authentication| IdP
RP -->|Tool discovery| RegistryMCP
RP -->|Web UI access| Registry
%% Connections from Gateway to MCP Servers
RP -->|SSE| MCP_Local1
RP -->|SSE| MCP_Local2
RP -->|SSE| MCP_EKS1
RP -->|SSE| MCP_EKS2
RP -->|Streamable HTTP| API_GW
%% Connections within API GW + Lambda
API_GW --> Lambda1
API_GW --> Lambda2
%% Connections to External Systems
MCP_Local1 -->|Tool Connection| DB1
MCP_Local2 -->|Tool Connection| DB2
MCP_EKS1 -->|Tool Connection| API1
MCP_EKS2 -->|Tool Connection| API2
Lambda1 -->|Tool Connection| API3
%% Style definitions
classDef user fill:#fff9c4,stroke:#f57f17,stroke-width:2px
classDef agent fill:#e1f5fe,stroke:#29b6f6,stroke-width:2px
classDef gateway fill:#e8f5e9,stroke:#66bb6a,stroke-width:2px
classDef nginx fill:#f3e5f5,stroke:#ab47bc,stroke-width:2px
classDef mcpServer fill:#fff3e0,stroke:#ffa726,stroke-width:2px
classDef eks fill:#ede7f6,stroke:#7e57c2,stroke-width:2px
classDef apiGw fill:#fce4ec,stroke:#ec407a,stroke-width:2px
classDef lambda fill:#ffebee,stroke:#ef5350,stroke-width:2px
classDef dataSource fill:#e3f2fd,stroke:#2196f3,stroke-width:2px
%% Apply styles
class User1,User2,UserN user
class Agent1,Agent2,Agent3,AgentN agent
class EC2_Gateway,NGINX gateway
class RP nginx
class AuthServer,Registry,RegistryMCP gateway
class IdP apiGw
class MCP_Local1,MCP_Local2 mcpServer
class EKS_Cluster,MCP_EKS1,MCP_EKS2 eks
class API_GW apiGw
class Lambda1,Lambda2 lambda
class DB1,DB2,API1,API2,API3 dataSourceKey Architectural Benefits:
- Unified Gateway: Single point of access for both AI agents and human developers through coding assistants
- Dual Authentication: Supports both human user authentication and machine-to-machine agent authentication
- Scalable Infrastructure: Nginx reverse proxy with horizontal scaling capabilities
- Multiple Transports: SSE and Streamable HTTP support for different client requirements
- OAuth 2.0/3.0 compliance with IdP integration
- Fine-grained access control at tool and method level
- Zero-trust network architecture
- Complete audit trails and comprehensive analytics for compliance
- Single configuration works across autonomous AI agents and AI coding assistants (VS Code, Cursor, Claude Code, Cline)
- Dynamic tool discovery with natural language queries for both agents and humans
- Instant onboarding for new team members and AI agent deployments
- Unified governance for both AI agents and human developers
- Container-native (Docker/Kubernetes)
- Real-time health monitoring and alerting
- Dual authentication supporting both human and machine authentication
There are 3 options for setting up the MCP Gateway & Registry:
- Option A: Pre-built Images — Fastest setup using pre-built Docker or Podman containers. Recommended for most users.
- Option B: Podman (Rootless) — Detailed Podman-specific instructions for macOS and rootless Linux environments.
- Option C: Build from Source — Full source build for customization or development.
Get running with pre-built Docker containers in minutes. This is the recommended approach for most users.
# Clone and configure
git clone https://github.com/agentic-community/mcp-gateway-registry.git
cd mcp-gateway-registry
cp .env.example .env
# Edit .env with your passwords (KEYCLOAK_ADMIN_PASSWORD, etc.)
nano .env
# Deploy with pre-built images
export DOCKERHUB_ORG=mcpgateway
./build_and_run.sh --prebuilt
# Access the Registry UI
open http://localhost:7860 # macOS
# xdg-open http://localhost:7860 # LinuxComplete Quick Start Guide - Full step-by-step instructions including:
- Prerequisites installation (Docker, Python, UV)
- Environment configuration
- MongoDB and Keycloak initialization
- User and service account setup
- Server and agent registration
- Testing the gateway functionality
Benefits: No build time | No Node.js required | No frontend compilation | Consistent tested images
Perfect for macOS and rootless Linux environments
Podman provides rootless container execution without requiring privileged ports, making it ideal for:
- macOS users with Podman Desktop
- Linux users preferring rootless containers
- Development environments where Docker daemon isn't available
Quick Podman Setup (macOS non-Apple Silicon):
# Install Podman Desktop
brew install podman-desktop
# OR download from: https://podman-desktop.io/Inside Podman Desktop, go to Preferences > Podman Machine and create a new machine with at least 4 CPUs and 8GB RAM. Alternatively, see more detailed Podman installation guide for instructions on setting this up on CLI.
# Initialize Podman machine
podman machine init
podman machine start
# Verify installation
podman --version
podman compose version
# Configure environment
cp .env.example .env
# Edit .env with your credentialsDeploy with Podman see full Podman setup instructions (downloading, installing, and initializing a first Podman container, as well as troubleshooting) in our Installation Guide.
Build with Podman:
# Auto-detect (will use Podman if Docker not available)
./build_and_run.sh --prebuilt
# Explicit Podman mode (only non-Apple Silicon)
./build_and_run.sh --prebuilt --podman
# Access registry at non-privileged ports
# On macOS:
open http://localhost:8080
# On Linux: xdg-open http://localhost:8080Note: Apple Silicon (M1/M2/M3)? Don't use
--prebuiltwith Podman on ARM64. This will cause a "proxy already running" error. See Podman on Apple Silicon Guide.
# To run on Apple Silicon Macs:
./build_and_run.sh --podmanKey Differences vs. Docker:
- No root/sudo required
- Works on macOS without privileged port access
- HTTP port:
8080(instead of80) - HTTPS port:
8443(instead of443) - All other service ports unchanged
For detailed Podman setup instructions, see Installation Guide and macOS Setup Guide.
New to MCP Gateway? Start with our Complete Setup Guide for detailed step-by-step instructions from scratch on AWS EC2.
Running on macOS? See our macOS Setup Guide for platform-specific instructions and optimizations.
Test Suite: The project includes comprehensive automated testing with pytest:
# Run all tests
make test
# Run only unit tests (fast)
make test-unit
# Run with coverage report
make test-coverage
# Run specific test categories
uv run pytest -m unit # Unit tests only
uv run pytest -m integration # Integration tests
uv run pytest -m "not slow" # Skip slow testsTest Structure:
-
Unit Tests (
tests/unit/) - Fast, isolated component tests -
Integration Tests (
tests/integration/) - Component interaction tests -
E2E Tests (
tests/integration/test_e2e_workflows.py) - Complete workflow tests
Python Agent:
-
agents/agent.py- Full-featured Python agent with advanced AI capabilities
Testing Documentation:
- Testing Guide - Comprehensive testing documentation
- Writing Tests - How to write effective tests
- Test Maintenance - Maintaining test suite health
Pre-commit Hooks:
# Install pre-commit hooks
pip install pre-commit
pre-commit install
# Run hooks manually
pre-commit run --all-filesNext Steps: Complete Installation Guide | Authentication Setup | AI Assistant Integration
Transform how both autonomous AI agents and development teams access enterprise tools with centralized governance:

Enterprise-curated MCP servers accessible through unified gateway |

AI assistants executing approved enterprise tools with governance |
|
Comprehensive real-time metrics and monitoring through Grafana dashboards with dual-path storage: SQLite for detailed historical analysis and OpenTelemetry (OTEL) export for integration with Prometheus, CloudWatch, Datadog, and other monitoring platforms. Track authentication events, tool executions, discovery queries, and system performance metrics. Learn more 
Real-time metrics and observability dashboard tracking server health, tool usage, and authentication events |
|
Seamlessly integrate with Anthropic's official MCP Registry to import and access curated MCP servers through your gateway:
- Import Servers: Select and import desired servers from Anthropic's registry with a single command
- Unified Access: Access imported servers through your gateway with centralized authentication and governance
- API Compatibility: Full support for Anthropic's Registry REST API specification - point your Anthropic API clients to this registry to discover available servers
Import and access curated MCP servers from Anthropic's official registry
Import Guide | Registry API Documentation
Unified Multi-Registry Access:
-
Anthropic MCP Registry - Import curated MCP servers with purple
ANTHROPICvisual tags -
Workday ASOR - Import AI agents from Agent System of Record with orange
ASORvisual tags - Automatic Sync - Scheduled synchronization with external registries
- Visual Identification - Clear visual tags distinguish federation sources in the UI
- Centralized Management - Single control plane for all federated servers and agents
Quick Setup:
# Configure federation sources
echo 'ASOR_ACCESS_TOKEN=your_token' >> .env
# Update federation.json with your sources
# Restart services
./build_and_run.sh📖 Complete Federation Guide - Environment setup, authentication, configuration, and troubleshooting
Integrated Vulnerability Detection:
- Automated Security Scanning - Integrated vulnerability scanning for MCP servers using Cisco AI Defence MCP Scanner, with automatic scans during registration and support for periodic registry-wide scans
- Detailed Security Reports - Comprehensive markdown reports with vulnerability details, severity assessments, and remediation recommendations
- Automatic Protection - Servers with security issues are automatically disabled with security-pending status to protect your infrastructure
- Compliance Ready - Security audit trails and vulnerability tracking for enterprise compliance requirements
Multiple Identity Modes:
- Machine-to-Machine (M2M) - For autonomous AI agents and automated systems
- Three-Legged OAuth (3LO) - For external service integration (Atlassian, Google, GitHub)
- Session-Based - For human developers using AI coding assistants and web interface
Supported Identity Providers: Keycloak, Amazon Cognito, and any OAuth 2.0 compatible provider. Learn more
Fine-Grained Permissions: Tool-level, method-level, team-based, and temporary access controls. Learn more
Cloud Platforms: Amazon EC2, Amazon EKS
Production-ready deployment on Amazon ECS Fargate with comprehensive enterprise features:
- Multi-AZ Architecture - High availability across multiple availability zones
- Application Load Balancer - HTTPS/SSL termination with automatic certificate management via ACM
- Auto-scaling - Dynamic scaling based on CPU and memory utilization
- CloudWatch Integration - Comprehensive monitoring, logging, and alerting
- NAT Gateway HA - High-availability NAT gateway configuration for secure outbound connectivity
- Keycloak Integration - Enterprise authentication with RDS Aurora PostgreSQL backend
- EFS Shared Storage - Persistent storage for models, logs, and configuration
- Service Discovery - AWS Cloud Map for service-to-service communication
Complete ECS Deployment Guide - Step-by-step instructions for deploying the entire stack with Terraform.
Coming Soon - Kubernetes deployment on Amazon EKS with Helm charts for container orchestration at scale.
| Getting Started | Enterprise Setup | Developer & Operations |
|---|---|---|
|
Complete Setup Guide NEW! Step-by-step from scratch on AWS EC2 |
Authentication Guide OAuth and identity provider integration |
AI Coding Assistants Setup VS Code, Cursor, Claude Code integration |
|
Installation Guide Complete setup instructions for EC2 and EKS |
AWS ECS Deployment Production-ready deployment on AWS ECS Fargate |
API Reference Programmatic registry management |
|
Keycloak Integration Enterprise identity with agent audit trails |
Token Refresh Service Automated token refresh and lifecycle management |
MCP Registry CLI Command-line client for registry management |
|
Configuration Reference Environment variables and settings |
Amazon Cognito Setup Step-by-step IdP configuration |
Observability Guide NEW! Metrics, monitoring, and OpenTelemetry setup |
|
Anthropic Registry Import NEW! Import servers from Anthropic MCP Registry |
Federation Guide External registry integration (Anthropic, ASOR) |
|
|
P2P Federation Guide NEW! Peer-to-peer registry federation |
||
|
Service Management Server lifecycle and operations |
Anthropic Registry API NEW! REST API compatibility |
|
|
Fine-Grained Access Control Permission management and security |
||
|
Dynamic Tool Discovery Autonomous agent capabilities |
||
|
Production Deployment Complete setup for production environments |
||
|
Troubleshooting Guide Common issues and solutions |
Join the Discussion
- GitHub Discussions - Feature requests and general discussion
- GitHub Issues - Bug reports and feature requests
Contributing
- Contributing Guide - How to contribute code and documentation
- Code of Conduct - Community guidelines
- Security Policy - Responsible disclosure process
Our development roadmap is organized into weekly milestones with clear deliverables and progress tracking:
| Milestone | Due Date | Progress | Status | Key Issues |
|---|---|---|---|---|
| January 2026 Week 3 | 2026-01-23 | 50% (1/2) | 🚧 In Progress |
Open: #295 - Multi-Level Rate Limiting Closed: #316 - Entra ID IAM APIs |
| January 2026 Week 4 | 2026-01-30 | 0% (0/3) | 📅 Planned | Open: #269 - AgentCore IAM Authentication, #260 - Federation Between Registries, #129 - Virtual MCP Server Support |
| Parking Lot | — | 100% (2/2) | 🗂️ Backlog | Closed: #316 - Entra ID IAM APIs, #315 - Distroless Docker Images |
Status Legend: 🚧 In Progress • 📅 Planned • 🗂️ Backlog • ✅ Complete
The following major features span multiple milestones and represent significant architectural improvements:
-
#129 - Virtual MCP Server Support 🚧 IN PROGRESS (Jan 2026 Week 3) Dynamic tool aggregation and intelligent routing using Lua/JavaScript scripting. Enables logical grouping of tools from multiple backend servers.
-
#232 - A2A Curated Registry Discovery ✅ COMPLETED Enable agent-to-agent discovery and tool invocation through curated registry patterns.
-
#260 - Federation Between MCP Registry Instances 🚧 IN PROGRESS Support for federated registry discovery and access across multiple registry instances. UI implementation complete.
-
#295 - Multi-Level Tool Usage Rate Limiting 📅 PLANNED (Jan 2026 Week 3) Comprehensive rate limiting architecture with detailed implementation guide for tool usage control.
-
#297 - Unified UI Registration Flow ✅ COMPLETED Streamlined registration experience for both MCP servers and A2A agents through a unified interface.
-
#316 - Entra ID IAM APIs ✅ COMPLETED Full IAM support for Microsoft Entra ID with harmonized API for user/group management. Includes M2M service accounts, self-signed JWT tokens, and fine-grained access control through scopes. Authentication Design | Scopes Management
-
#297 - Unified UI Registration Flow ✅ COMPLETED Streamlined registration experience for both MCP servers and A2A agents through a unified interface.
-
#232 - A2A Curated Registry Discovery ✅ COMPLETED Agent-to-agent discovery and tool invocation through curated registry patterns.
-
#329 - Update llms.txt ✅ COMPLETED (v1.0.9) Updated AI assistant reference documentation with recent architecture changes.
-
#221 - DocumentDB Implementation ✅ COMPLETED (v1.0.9) Production-grade distributed storage with MongoDB/DocumentDB backend implementation.
-
#70 - Docker Build & Runtime Performance Optimization ✅ COMPLETED (v1.0.9) Multi-stage Docker builds with 66-80% image size reduction.
-
#287 - Filter Sidebar Buttons ✅ COMPLETED Fixed filter buttons to properly filter both MCP servers and A2A agent cards.
-
#284 - Statistics Count Fix ✅ COMPLETED Sidebar statistics now correctly count both MCP servers and A2A agents.
-
#259 - Simplify JWT Token Generation ✅ COMPLETED Streamlined JWT token generation process in Registry UI.
-
#315 - Distroless Docker Images ✅ COMPLETED Security hardening through migration to distroless/hardened base images.
For the complete list of all issues, feature requests, and detailed release history, visit:
This project is licensed under the Apache-2.0 License - see the LICENSE file for details.
⭐ Star this repository if it helps your organization!
For Tasks:
Click tags to check more tools for each tasksFor Jobs:
Alternative AI tools for mcp-gateway-registry
Similar Open Source Tools
mcp-gateway-registry
The MCP Gateway & Registry is a unified, enterprise-ready platform that centralizes access to both MCP Servers and AI Agents using the Model Context Protocol (MCP). It serves as a Unified MCP Server Gateway, MCP Servers Registry, and Agent Registry & A2A Communication Hub. The platform integrates with external registries, providing a single control plane for tool access, agent orchestration, and communication patterns. It transforms the chaos of managing individual MCP server configurations into an organized approach with secure, governed access to curated servers and registered agents. The platform supports dynamic tool discovery, autonomous agent communication, and unified policies for server and agent access.

ramparts
Ramparts is a fast, lightweight security scanner designed for the Model Context Protocol (MCP) ecosystem. It scans MCP servers to identify vulnerabilities and provides security features such as discovering capabilities, multi-transport support, session management, static analysis, cross-origin analysis, LLM-powered analysis, and risk assessment. The tool is suitable for developers, MCP users, and MCP developers to ensure the security of their connections. It can be used for security audits, development testing, CI/CD integration, and compliance with security requirements for AI agent deployments.
BioAgents
BioAgents AgentKit is an advanced AI agent framework tailored for biological and scientific research. It offers powerful conversational AI capabilities with specialized knowledge in biology, life sciences, and scientific research methodologies. The framework includes state-of-the-art analysis agents, configurable research agents, and a variety of specialized agents for tasks such as file parsing, research planning, literature search, data analysis, hypothesis generation, research reflection, and user-facing responses. BioAgents also provides support for LLM libraries, multiple search backends for literature agents, and two backends for data analysis. The project structure includes backend source code, services for chat, job queue system, real-time notifications, and JWT authentication, as well as a frontend UI built with Preact.
lyraios
LYRAIOS (LLM-based Your Reliable AI Operating System) is an advanced AI assistant platform built with FastAPI and Streamlit, designed to serve as an operating system for AI applications. It offers core features such as AI process management, memory system, and I/O system. The platform includes built-in tools like Calculator, Web Search, Financial Analysis, File Management, and Research Tools. It also provides specialized assistant teams for Python and research tasks. LYRAIOS is built on a technical architecture comprising FastAPI backend, Streamlit frontend, Vector Database, PostgreSQL storage, and Docker support. It offers features like knowledge management, process control, and security & access control. The roadmap includes enhancements in core platform, AI process management, memory system, tools & integrations, security & access control, open protocol architecture, multi-agent collaboration, and cross-platform support.
astron-rpa
AstronRPA is an enterprise-grade Robotic Process Automation (RPA) desktop application that supports low-code/no-code development. It enables users to rapidly build workflows and automate desktop software and web pages. The tool offers comprehensive automation support for various applications, highly component-based design, enterprise-grade security and collaboration features, developer-friendly experience, native agent empowerment, and multi-channel trigger integration. It follows a frontend-backend separation architecture with components for system operations, browser automation, GUI automation, AI integration, and more. The tool is deployed via Docker and designed for complex RPA scenarios.
shannon
Shannon is an AI pentester that delivers actual exploits, not just alerts. It autonomously hunts for attack vectors in your code, then uses its built-in browser to execute real exploits, such as injection attacks, and auth bypass, to prove the vulnerability is actually exploitable. Shannon closes the security gap by acting as your on-demand whitebox pentester, providing concrete proof of vulnerabilities to let you ship with confidence. It is a core component of the Keygraph Security and Compliance Platform, automating penetration testing and compliance journey. Shannon Lite achieves a 96.15% success rate on a hint-free, source-aware XBOW benchmark.
llmos
LLMos is an operating system designed for physical AI agents, providing a hybrid runtime environment where AI agents can perceive, reason, act on hardware, and evolve over time locally without cloud dependency. It allows natural language programming, dual-brain architecture for fast instinct and deep planner brains, markdown-as-code for defining agents and skills, and supports swarm intelligence and cognitive world models. The tool is built on a tech stack including Next.js, Electron, Python, and WebAssembly, and is structured around a dual-brain cognitive architecture, volume system, HAL for hardware abstraction, applet system for dynamic UI, and dreaming & evolution for robot improvement. The project is in Phase 1 (Foundation) and aims to move into Phase 2 (Dual-Brain & Local Intelligence), with contributions welcomed under the Apache 2.0 license by Evolving Agents Labs.
sandboxed.sh
sandboxed.sh is a self-hosted cloud orchestrator for AI coding agents that provides isolated Linux workspaces with Claude Code, OpenCode & Amp runtimes. It allows users to hand off entire development cycles, run multi-day operations unattended, and keep sensitive data local by analyzing data against scientific literature. The tool features dual runtime support, mission control for remote agent management, isolated workspaces, a git-backed library, MCP registry, and multi-platform support with a web dashboard and iOS app.
ccprompts
ccprompts is a collection of ~70 Claude Code commands for software development workflows with agent generation capabilities. It includes safety validation and can be used directly with Claude Code or adapted for specific needs. The agent template system provides a wizard for creating specialized sub-agents (e.g., security auditors, systems architects) with standardized formatting and proper tool access. The repository is under active development, so caution is advised when using it in production environments.
heurist-agent-framework
Heurist Agent Framework is a flexible multi-interface AI agent framework that allows processing text and voice messages, generating images and videos, interacting across multiple platforms, fetching and storing information in a knowledge base, accessing external APIs and tools, and composing complex workflows using Mesh Agents. It supports various platforms like Telegram, Discord, Twitter, Farcaster, REST API, and MCP. The framework is built on a modular architecture and provides core components, tools, workflows, and tool integration with MCP support.
chatnio
Chat Nio is a next-generation AIGC one-stop business solution that combines the advantages of frontend-oriented lightweight deployment projects with powerful API distribution systems. It offers rich model support, beautiful UI design, complete Markdown support, multi-theme support, internationalization support, text-to-image support, powerful conversation sync, model market & preset system, rich file parsing, full model internet search, Progressive Web App (PWA) support, comprehensive backend management, multiple billing methods, innovative model caching, and additional features. The project aims to address limitations in conversation synchronization, billing, file parsing, conversation URL sharing, channel management, and API call support found in existing AIGC commercial sites, while also providing a user-friendly interface design and C-end features.
CortexON
CortexON is an open-source, multi-agent AI system designed to automate and simplify everyday tasks. It integrates specialized agents like Web Agent, File Agent, Coder Agent, Executor Agent, and API Agent to accomplish user-defined objectives. CortexON excels at executing complex workflows, research tasks, technical operations, and business process automations by dynamically coordinating the agents' unique capabilities. It offers advanced research automation, multi-agent orchestration, integration with third-party APIs, code generation and execution, efficient file and data management, and personalized task execution for travel planning, market analysis, educational content creation, and business intelligence.
persistent-ai-memory
Persistent AI Memory System is a comprehensive tool that offers persistent, searchable storage for AI assistants. It includes features like conversation tracking, MCP tool call logging, and intelligent scheduling. The system supports multiple databases, provides enhanced memory management, and offers various tools for memory operations, schedule management, and system health checks. It also integrates with various platforms like LM Studio, VS Code, Koboldcpp, Ollama, and more. The system is designed to be modular, platform-agnostic, and scalable, allowing users to handle large conversation histories efficiently.
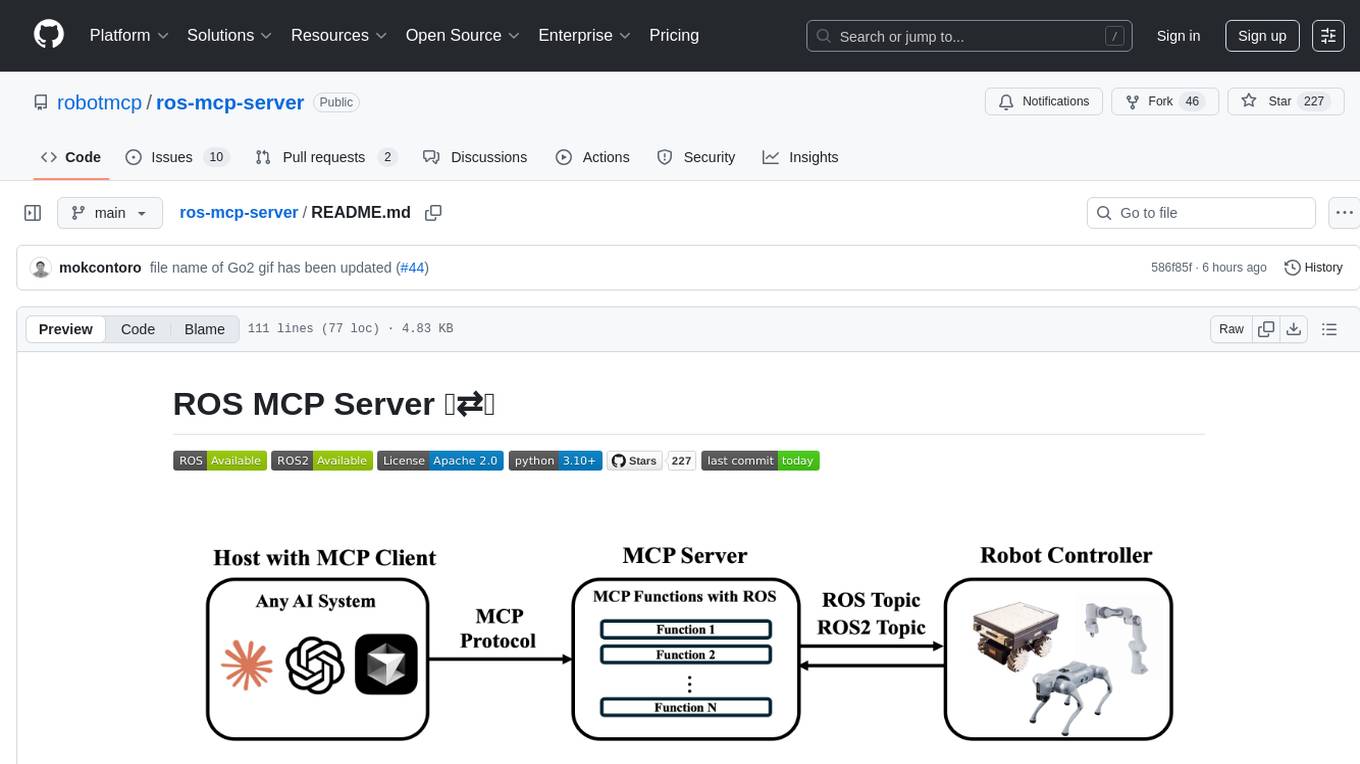
ros-mcp-server
The ros-mcp-server repository contains a ROS (Robot Operating System) package that provides a server for Multi-Contact Planning (MCP) in robotics. The server facilitates the planning of multiple contacts between a robot and its environment, enabling complex manipulation tasks. It includes functionalities for collision checking, motion planning, and contact stability analysis. This tool is designed to enhance the capabilities of robotic systems by enabling them to perform tasks that involve multiple points of contact with the environment. The repository includes documentation and examples to help users integrate the MCP server into their robotic applications.
databend
Databend is an open-source cloud data warehouse built in Rust, offering fast query execution and data ingestion for complex analysis of large datasets. It integrates with major cloud platforms, provides high performance with AI-powered analytics, supports multiple data formats, ensures data integrity with ACID transactions, offers flexible indexing options, and features community-driven development. Users can try Databend through a serverless cloud or Docker installation, and perform tasks such as data import/export, querying semi-structured data, managing users/databases/tables, and utilizing AI functions.
abi
ABI (Agentic Brain Infrastructure) is a Python-based AI Operating System designed to serve as the core infrastructure for building an Agentic AI Ontology Engine. It empowers organizations to integrate, manage, and scale AI-driven operations with multiple AI models, focusing on ontology, agent-driven workflows, and analytics. ABI emphasizes modularity and customization, providing a customizable framework aligned with international standards and regulatory frameworks. It offers features such as configurable AI agents, ontology management, integrations with external data sources, data processing pipelines, workflow automation, analytics, and data handling capabilities.
For similar tasks
mcp-gateway-registry
The MCP Gateway & Registry is a unified, enterprise-ready platform that centralizes access to both MCP Servers and AI Agents using the Model Context Protocol (MCP). It serves as a Unified MCP Server Gateway, MCP Servers Registry, and Agent Registry & A2A Communication Hub. The platform integrates with external registries, providing a single control plane for tool access, agent orchestration, and communication patterns. It transforms the chaos of managing individual MCP server configurations into an organized approach with secure, governed access to curated servers and registered agents. The platform supports dynamic tool discovery, autonomous agent communication, and unified policies for server and agent access.
superagent-py
Superagent is an open-source framework that enables developers to integrate production-ready AI assistants into any application quickly and easily. It provides a Python SDK for interacting with the Superagent API, allowing developers to create, manage, and invoke AI agents. The SDK simplifies the process of building AI-powered applications, making it accessible to developers of all skill levels.
AGiXT
AGiXT is a dynamic Artificial Intelligence Automation Platform engineered to orchestrate efficient AI instruction management and task execution across a multitude of providers. Our solution infuses adaptive memory handling with a broad spectrum of commands to enhance AI's understanding and responsiveness, leading to improved task completion. The platform's smart features, like Smart Instruct and Smart Chat, seamlessly integrate web search, planning strategies, and conversation continuity, transforming the interaction between users and AI. By leveraging a powerful plugin system that includes web browsing and command execution, AGiXT stands as a versatile bridge between AI models and users. With an expanding roster of AI providers, code evaluation capabilities, comprehensive chain management, and platform interoperability, AGiXT is consistently evolving to drive a multitude of applications, affirming its place at the forefront of AI technology.
infra
E2B Infra is a cloud runtime for AI agents. It provides SDKs and CLI to customize and manage environments and run AI agents in the cloud. The infrastructure is deployed using Terraform and is currently only deployable on GCP. The main components of the infrastructure are the API server, daemon running inside instances (sandboxes), Nomad driver for managing instances (sandboxes), and Nomad driver for building environments (templates).
Awesome-European-Tech
Awesome European Tech is an up-to-date list of recommended European projects and companies curated by the community to support and strengthen the European tech ecosystem. It focuses on privacy and sustainability, showcasing companies that adhere to GDPR compliance and sustainability standards. The project aims to highlight and support European startups and projects excelling in privacy, sustainability, and innovation to contribute to a more diverse, resilient, and interconnected global tech landscape.

LarAgent
LarAgent is a framework designed to simplify the creation and management of AI agents within Laravel projects. It offers an Eloquent-like syntax for creating and managing AI agents, Laravel-style artisan commands, flexible agent configuration, structured output handling, image input support, and extensibility. LarAgent supports multiple chat history storage options, custom tool creation, event system for agent interactions, multiple provider support, and can be used both in Laravel and standalone environments. The framework is constantly evolving to enhance developer experience, improve AI capabilities, enhance security and storage features, and enable advanced integrations like provider fallback system, Laravel Actions integration, and voice chat support.
agent-squad
Agent Squad is a flexible, lightweight open-source framework for orchestrating multiple AI agents to handle complex conversations. It intelligently routes queries, maintains context across interactions, and offers pre-built components for quick deployment. The system allows easy integration of custom agents and conversation messages storage solutions, making it suitable for various applications from simple chatbots to sophisticated AI systems, scaling efficiently.
boxlite
BoxLite is an embedded, lightweight micro-VM runtime designed for AI agents running OCI containers with hardware-level isolation. It is built for high concurrency with no daemon required, offering features like lightweight VMs, high concurrency, hardware isolation, embeddability, and OCI compatibility. Users can spin up 'Boxes' to run containers for AI agent sandboxes and multi-tenant code execution scenarios where Docker alone is insufficient and full VM infrastructure is too heavy. BoxLite supports Python, Node.js, and Rust with quick start guides for each, along with features like CPU/memory limits, storage options, networking capabilities, security layers, and image registry configuration. The tool provides SDKs for Python and Node.js, with Go support coming soon. It offers detailed documentation, examples, and architecture insights for users to understand how BoxLite works under the hood.
For similar jobs
promptflow
**Prompt flow** is a suite of development tools designed to streamline the end-to-end development cycle of LLM-based AI applications, from ideation, prototyping, testing, evaluation to production deployment and monitoring. It makes prompt engineering much easier and enables you to build LLM apps with production quality.
deepeval
DeepEval is a simple-to-use, open-source LLM evaluation framework specialized for unit testing LLM outputs. It incorporates various metrics such as G-Eval, hallucination, answer relevancy, RAGAS, etc., and runs locally on your machine for evaluation. It provides a wide range of ready-to-use evaluation metrics, allows for creating custom metrics, integrates with any CI/CD environment, and enables benchmarking LLMs on popular benchmarks. DeepEval is designed for evaluating RAG and fine-tuning applications, helping users optimize hyperparameters, prevent prompt drifting, and transition from OpenAI to hosting their own Llama2 with confidence.
MegaDetector
MegaDetector is an AI model that identifies animals, people, and vehicles in camera trap images (which also makes it useful for eliminating blank images). This model is trained on several million images from a variety of ecosystems. MegaDetector is just one of many tools that aims to make conservation biologists more efficient with AI. If you want to learn about other ways to use AI to accelerate camera trap workflows, check out our of the field, affectionately titled "Everything I know about machine learning and camera traps".
leapfrogai
LeapfrogAI is a self-hosted AI platform designed to be deployed in air-gapped resource-constrained environments. It brings sophisticated AI solutions to these environments by hosting all the necessary components of an AI stack, including vector databases, model backends, API, and UI. LeapfrogAI's API closely matches that of OpenAI, allowing tools built for OpenAI/ChatGPT to function seamlessly with a LeapfrogAI backend. It provides several backends for various use cases, including llama-cpp-python, whisper, text-embeddings, and vllm. LeapfrogAI leverages Chainguard's apko to harden base python images, ensuring the latest supported Python versions are used by the other components of the stack. The LeapfrogAI SDK provides a standard set of protobuffs and python utilities for implementing backends and gRPC. LeapfrogAI offers UI options for common use-cases like chat, summarization, and transcription. It can be deployed and run locally via UDS and Kubernetes, built out using Zarf packages. LeapfrogAI is supported by a community of users and contributors, including Defense Unicorns, Beast Code, Chainguard, Exovera, Hypergiant, Pulze, SOSi, United States Navy, United States Air Force, and United States Space Force.
llava-docker
This Docker image for LLaVA (Large Language and Vision Assistant) provides a convenient way to run LLaVA locally or on RunPod. LLaVA is a powerful AI tool that combines natural language processing and computer vision capabilities. With this Docker image, you can easily access LLaVA's functionalities for various tasks, including image captioning, visual question answering, text summarization, and more. The image comes pre-installed with LLaVA v1.2.0, Torch 2.1.2, xformers 0.0.23.post1, and other necessary dependencies. You can customize the model used by setting the MODEL environment variable. The image also includes a Jupyter Lab environment for interactive development and exploration. Overall, this Docker image offers a comprehensive and user-friendly platform for leveraging LLaVA's capabilities.

carrot
The 'carrot' repository on GitHub provides a list of free and user-friendly ChatGPT mirror sites for easy access. The repository includes sponsored sites offering various GPT models and services. Users can find and share sites, report errors, and access stable and recommended sites for ChatGPT usage. The repository also includes a detailed list of ChatGPT sites, their features, and accessibility options, making it a valuable resource for ChatGPT users seeking free and unlimited GPT services.
TrustLLM
TrustLLM is a comprehensive study of trustworthiness in LLMs, including principles for different dimensions of trustworthiness, established benchmark, evaluation, and analysis of trustworthiness for mainstream LLMs, and discussion of open challenges and future directions. Specifically, we first propose a set of principles for trustworthy LLMs that span eight different dimensions. Based on these principles, we further establish a benchmark across six dimensions including truthfulness, safety, fairness, robustness, privacy, and machine ethics. We then present a study evaluating 16 mainstream LLMs in TrustLLM, consisting of over 30 datasets. The document explains how to use the trustllm python package to help you assess the performance of your LLM in trustworthiness more quickly. For more details about TrustLLM, please refer to project website.
AI-YinMei
AI-YinMei is an AI virtual anchor Vtuber development tool (N card version). It supports fastgpt knowledge base chat dialogue, a complete set of solutions for LLM large language models: [fastgpt] + [one-api] + [Xinference], supports docking bilibili live broadcast barrage reply and entering live broadcast welcome speech, supports Microsoft edge-tts speech synthesis, supports Bert-VITS2 speech synthesis, supports GPT-SoVITS speech synthesis, supports expression control Vtuber Studio, supports painting stable-diffusion-webui output OBS live broadcast room, supports painting picture pornography public-NSFW-y-distinguish, supports search and image search service duckduckgo (requires magic Internet access), supports image search service Baidu image search (no magic Internet access), supports AI reply chat box [html plug-in], supports AI singing Auto-Convert-Music, supports playlist [html plug-in], supports dancing function, supports expression video playback, supports head touching action, supports gift smashing action, supports singing automatic start dancing function, chat and singing automatic cycle swing action, supports multi scene switching, background music switching, day and night automatic switching scene, supports open singing and painting, let AI automatically judge the content.







