Best AI tools for< Application Security Tester >
Infographic
20 - AI tool Sites
DryRun Security
DryRun Security is an AI-powered security tool designed to provide developers with security context and analysis for code changes in real-time. It offers a suite of analyzers to identify risky code changes, such as SQL injection, command injection, and sensitive file modifications. The tool integrates seamlessly with GitHub repositories, ensuring developers receive security feedback before merging code changes. DryRun Security aims to empower developers to write secure code efficiently and effectively.

MobiHeals
MobiHeals is a mobile application focused on security analysis and vulnerability checks for mobile apps. It offers comprehensive security vulnerability analysis, cloud-based static and dynamic application security testing, and integrated vulnerability assessment in one platform. MobiHeals helps users comply with global cybersecurity guidelines and manage security vulnerabilities throughout the development, testing, and operation stages of mobile applications.
Zivy
Zivy is an AI-powered communication tool designed to help Engineering and Product Leads manage and prioritize messages effectively. It transforms the chaotic Slack environment into organized stacks of cards, ensuring that users focus on what truly matters. Zivy's AI capabilities learn user preferences, prioritize important messages, and continuously improve efficiency. The application also emphasizes data security, encrypting messages, and adhering to strict privacy standards. Zivy aims to streamline communication processes and enhance productivity by reducing noise and optimizing message delivery.
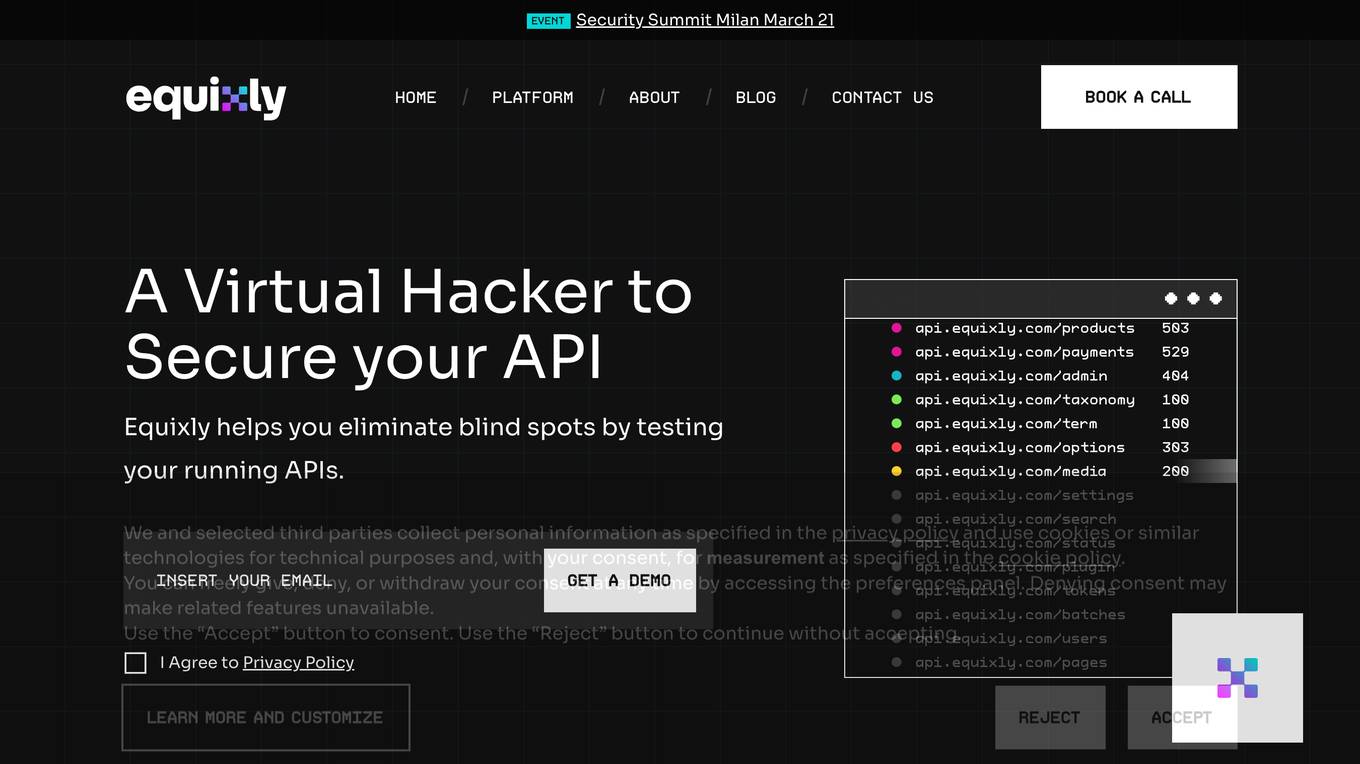
Equixly
Equixly is an AI-powered application designed to help secure APIs by identifying vulnerabilities and weaknesses through continuous security testing. It offers features such as scalable API PenTesting, rapid remediation, attack simulation, mapping attack surfaces, compliance simplification, and data exposure minimization. Equixly aims to provide users with a comprehensive solution to enhance the security of their APIs and streamline compliance processes.

Pentest Copilot
Pentest Copilot by BugBase is an ultimate ethical hacking assistant that guides users through each step of the hacking journey, from analyzing web apps to root shells. It eliminates redundant research, automates payload and command generation, and provides intelligent contextual analysis to save time. The application excels at data extraction, privilege escalation, lateral movement, and leaving no trace behind. With features like secure VPN integration, total control over sessions, parallel command processing, and flexibility to choose between local or cloud execution, Pentest Copilot offers a seamless and efficient hacking experience without the need for Kali Linux installation.
Ivie
Ivie is an AI-powered user research tool that automates the collection and analysis of qualitative user insights to help product teams build better products. It offers features such as AI-powered insights, processed user insights, in-depth analysis, automated follow-up questions, multilingual support, and more. Ivie provides advantages like human-like conversations, scalable surveys, customizable AI researchers, quick research setup, and multiple question types. However, it has disadvantages such as limited customization options, potential language barriers, and the need for user training. The frequently asked questions cover topics like supported research types, data security, multilingual research, and research findings presentation. Ivie is suitable for jobs related to user research, product development, customer satisfaction analysis, market research, and concept testing. The application can be used for tasks like conducting customer interviews, analyzing user feedback, creating surveys, synthesizing research findings, and building user personas.
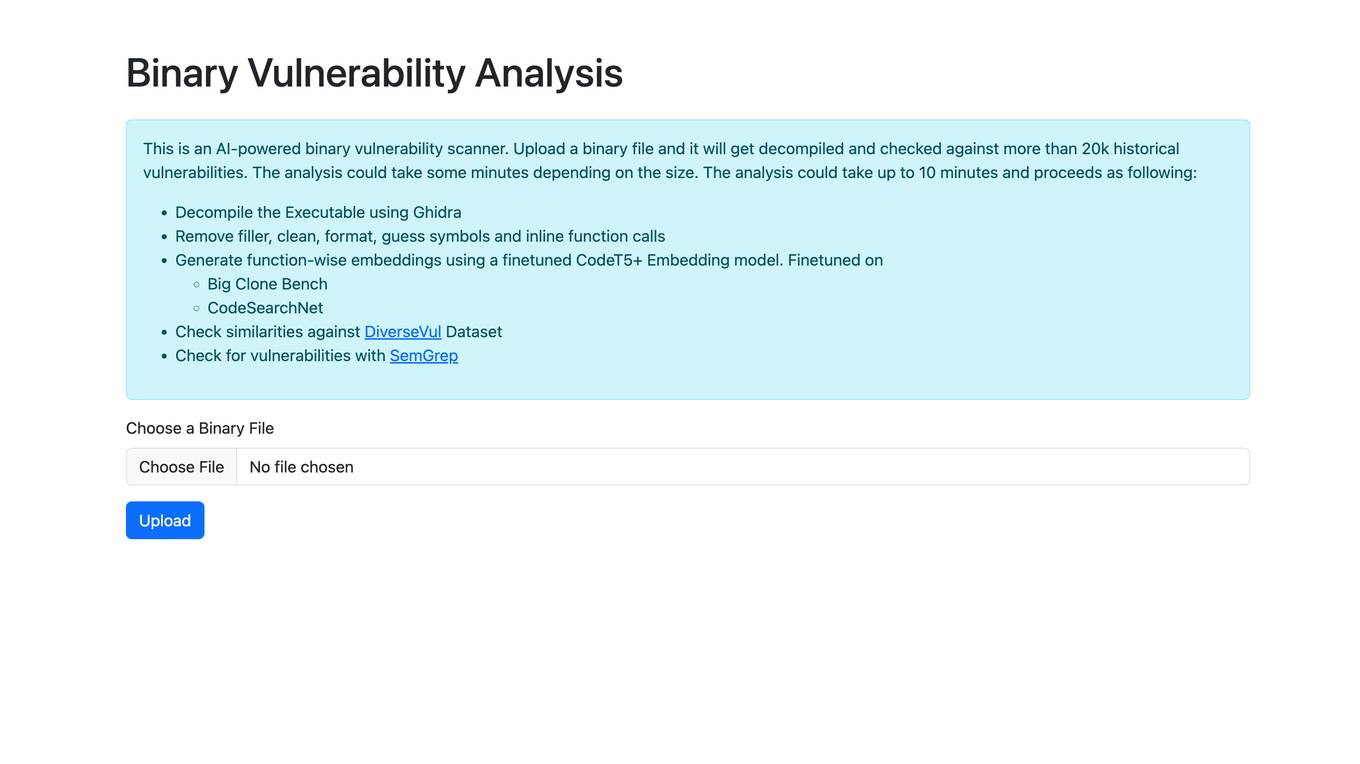
Binary Vulnerability Analysis
The website offers an AI-powered binary vulnerability scanner that allows users to upload a binary file for analysis. The tool decompiles the executable, removes filler, formats the code, and checks for vulnerabilities by comparing against a database of historical vulnerabilities. It utilizes a finetuned CodeT5+ Embedding model to generate function-wise embeddings and checks for similarities against the DiverseVul Dataset. The tool also uses SemGrep to identify vulnerabilities in the code.
Huntr
Huntr is the world's first bug bounty platform for AI/ML. It provides a single place for security researchers to submit vulnerabilities, ensuring the security and stability of AI/ML applications, including those powered by Open Source Software (OSS).
PerfAI
The website is an AI tool designed for API privacy, governance, and testing. It offers solutions to detect and remediate sensitive data leaks, ensure compliance, and automate API testing and documentation. The AI-driven platform is trained on 70k public APIs and provides features like AI detection, cataloging, remediation, and best practices for data collection and storage. It aims to streamline API development, enhance performance, and improve security for APIs and applications.
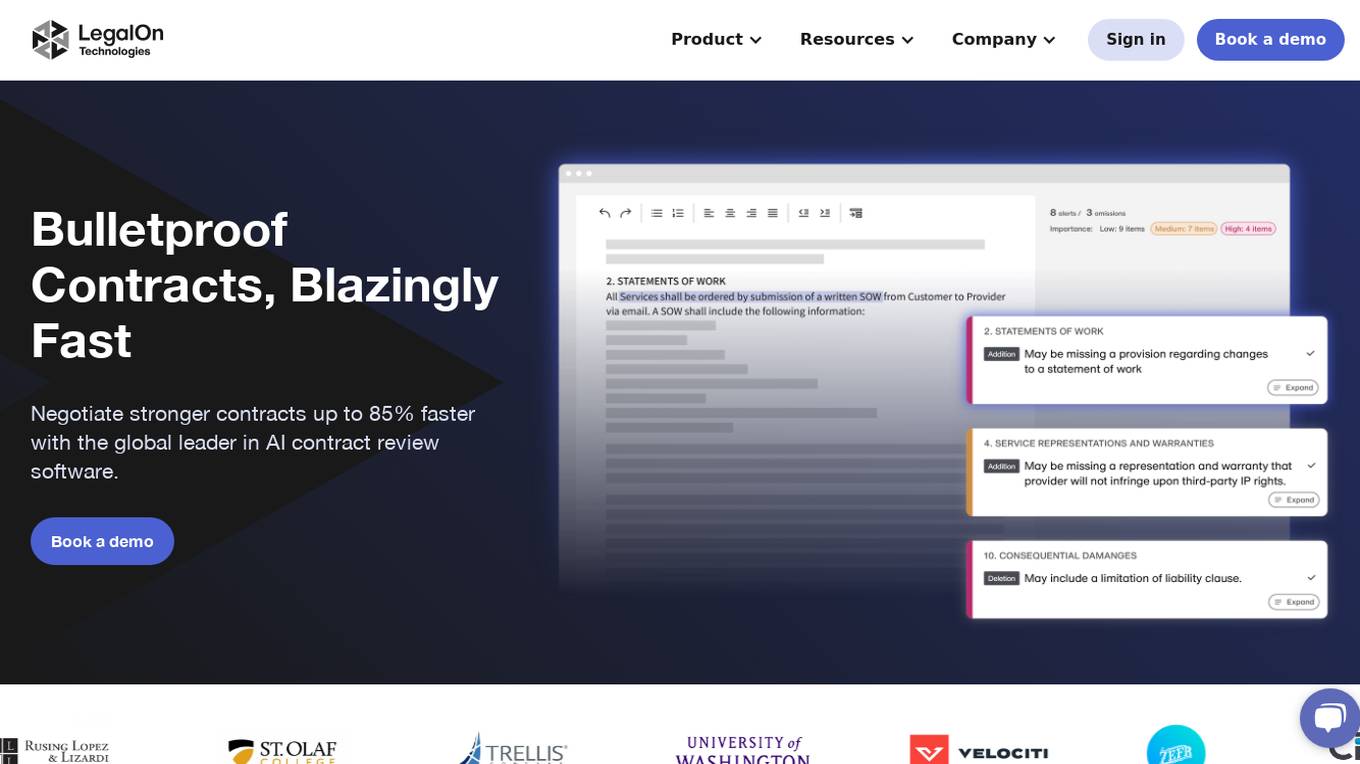
LegalOn Technologies
LegalOn Technologies is a global leader in AI contract review software, providing a platform that enables users to negotiate stronger contracts up to 85% faster. The application offers pre-built and custom AI playbooks, built by experienced attorneys, to ensure high-quality contract reviews. LegalOn's AI is anchored in attorney-written content and rigorously tested, providing accurate and up-to-date legal knowledge for reliable results. The platform is SOC 2 Type II certified, GDPR, and CCPA compliant, prioritizing security and privacy for user data.
CloudDefense.AI
CloudDefense.AI is an industry-leading multi-layered Cloud Native Application Protection Platform (CNAPP) that safeguards cloud infrastructure and cloud-native apps with expertise, precision, and confidence. It offers comprehensive cloud security solutions, vulnerability management, compliance, and application security testing. The platform utilizes advanced AI technology to proactively detect and analyze real-time threats, ensuring robust protection for businesses against cyber threats.

Start Left® Security
Start Left® Security is an AI-driven application security posture management platform that empowers product teams to automate secure-by-design software from people to cloud. The platform integrates security into every facet of the organization, offering a unified solution that aligns with business goals, fosters continuous improvement, and drives innovation. Start Left® Security provides a gamified DevSecOps experience with comprehensive security capabilities like SCA, SBOM, SAST, DAST, Container Security, IaC security, ASPM, and more.

AppSec Assistant
AppSec Assistant is an AI-powered application designed to provide automated security recommendations in Jira Cloud. It focuses on ensuring data security by enabling secure-by-design software development. The tool simplifies setup by allowing users to add their OpenAI API key and organization, encrypts and stores data using Atlassian's Storage API, and provides tailored security recommendations for each ticket to reduce manual AppSec reviews. AppSec Assistant empowers developers by keeping up with their pace and helps in easing the security review bottleneck.
Dynatrace
Dynatrace is a modern cloud platform that offers unified observability and security solutions to simplify cloud complexity and drive innovation. Powered by causal AI, Dynatrace provides analytics and automation capabilities to help businesses monitor and secure their full stack, solve digital challenges, and make better business decisions in real-time. Trusted by thousands of global brands, Dynatrace empowers teams to deliver flawless digital experiences, drive intelligent cloud ecosystem automations, and solve any use-case with custom solutions.
Endor Labs
Endor Labs is an AI-powered software supply chain security solution that helps organizations manage their software bills of materials (SBOM), secure their open source dependencies, optimize CI/CD pipeline security, and enhance application security with secret detection. The platform offers advanced features such as AI-assisted OSS selection, compliance management, reachability-based SCA, and repository security posture management. Endor Labs aims to streamline security processes, reduce false positives, and provide actionable insights to improve software supply chain security.
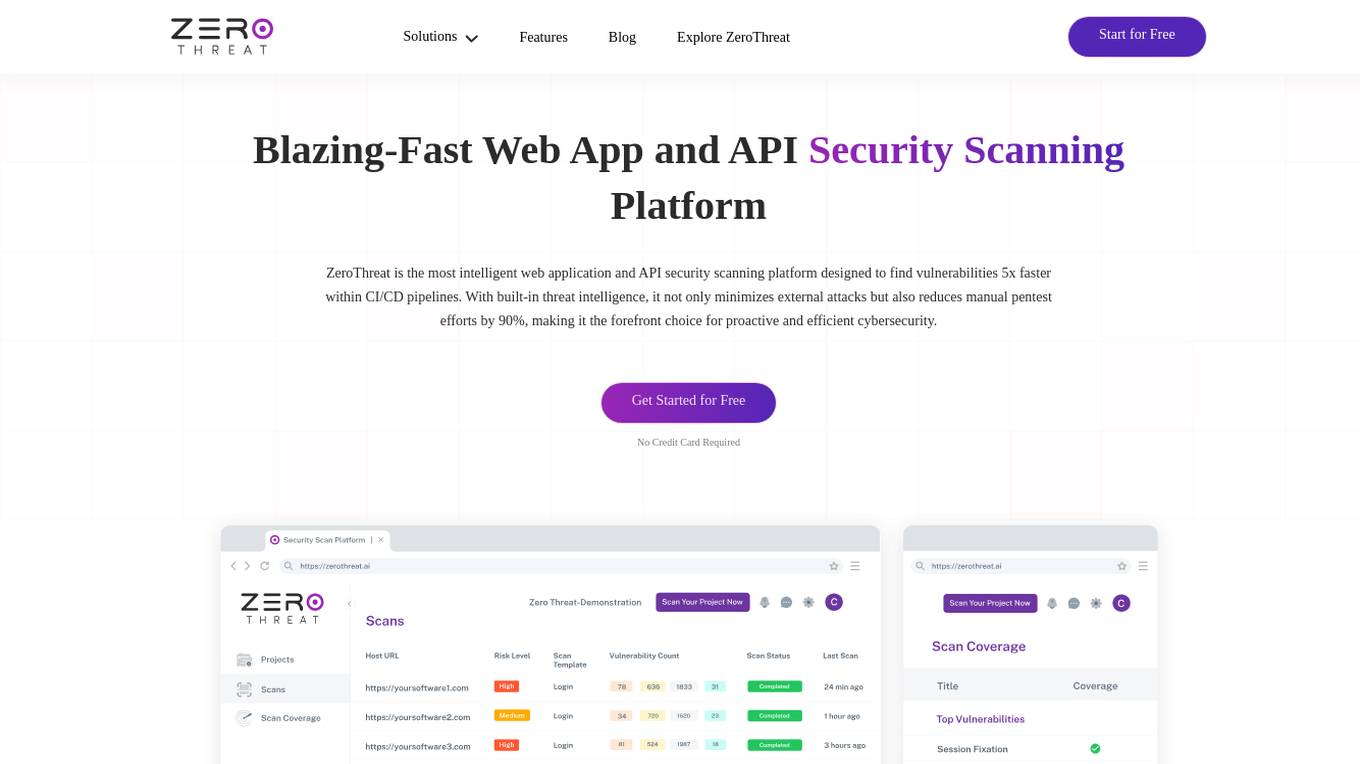
ZeroThreat
ZeroThreat is a web app and API security scanner that helps businesses identify and fix vulnerabilities in their web applications and APIs. It uses a combination of static and dynamic analysis techniques to scan for a wide range of vulnerabilities, including OWASP Top 10, CWE Top 25, and SANS Top 25. ZeroThreat also provides continuous monitoring and alerting, so businesses can stay on top of new vulnerabilities as they emerge.
Snyk
Snyk is a developer security platform powered by DeepCode AI, offering solutions for application security, software supply chain security, and secure AI-generated code. It provides comprehensive vulnerability data, license compliance management, and self-service security education. Snyk integrates AI models trained on security-specific data to secure applications and manage tech debt effectively. The platform ensures developer-first security with one-click security fixes and AI-powered recommendations, enhancing productivity while maintaining security standards.
Enterprise AI Solutions
The website is an AI tool that offers a wide range of AI, software, and tools for enterprise growth and automation. It provides solutions in areas such as AI hardware, automation, application security, CRM, cloud services, data management, generative AI, network monitoring, process intelligence, proxies, remote monitoring, surveys, sustainability, workload automation, and more. The platform aims to help businesses leverage AI technologies to enhance efficiency, security, and productivity across various industries.
Digital.ai
Digital.ai is an AI-powered DevOps platform that helps organizations automate software releases, improve mobile application testing and security, and provide insights across the software lifecycle. The platform includes a suite of products that can be used to manage the complexities of software delivery, including analytics and intelligence, enterprise agile planning, application protection and security, continuous testing, release orchestration, and deployment automation.

Mimecast
Mimecast is an AI-powered email and collaboration security application that offers advanced threat protection, cloud archiving, security awareness training, and more. With a focus on protecting communications, data, and people, Mimecast leverages AI technology to provide industry-leading security solutions to organizations globally. The application is designed to defend against sophisticated email attacks, enhance human risk management, and streamline compliance processes.
20 - Open Source Tools
ai-goat
AI Goat is a tool designed to help users learn about AI security through a series of vulnerable LLM CTF challenges. It allows users to run everything locally on their system without the need for sign-ups or cloud fees. The tool focuses on exploring security risks associated with large language models (LLMs) like ChatGPT, providing practical experience for security researchers to understand vulnerabilities and exploitation techniques. AI Goat uses the Vicuna LLM, derived from Meta's LLaMA and ChatGPT's response data, to create challenges that involve prompt injections, insecure output handling, and other LLM security threats. The tool also includes a prebuilt Docker image, ai-base, containing all necessary libraries to run the LLM and challenges, along with an optional CTFd container for challenge management and flag submission.
Awesome-Code-LLM
Analyze the following text from a github repository (name and readme text at end) . Then, generate a JSON object with the following keys and provide the corresponding information for each key, in lowercase letters: 'description' (detailed description of the repo, must be less than 400 words,Ensure that no line breaks and quotation marks.),'for_jobs' (List 5 jobs suitable for this tool,in lowercase letters), 'ai_keywords' (keywords of the tool,user may use those keyword to find the tool,in lowercase letters), 'for_tasks' (list of 5 specific tasks user can use this tool to do,in lowercase letters), 'answer' (in english languages)
Awesome-LLM4Cybersecurity
The repository 'Awesome-LLM4Cybersecurity' provides a comprehensive overview of the applications of Large Language Models (LLMs) in cybersecurity. It includes a systematic literature review covering topics such as constructing cybersecurity-oriented domain LLMs, potential applications of LLMs in cybersecurity, and research directions in the field. The repository analyzes various benchmarks, datasets, and applications of LLMs in cybersecurity tasks like threat intelligence, fuzzing, vulnerabilities detection, insecure code generation, program repair, anomaly detection, and LLM-assisted attacks.
PentestGPT
PentestGPT provides advanced AI and integrated tools to help security teams conduct comprehensive penetration tests effortlessly. Scan, exploit, and analyze web applications, networks, and cloud environments with ease and precision, without needing expert skills. The tool utilizes Supabase for data storage and management, and Vercel for hosting the frontend. It offers a local quickstart guide for running the tool locally and a hosted quickstart guide for deploying it in the cloud. PentestGPT aims to simplify the penetration testing process for security professionals and enthusiasts alike.
Academic_LLM_Sec_Papers
Academic_LLM_Sec_Papers is a curated collection of academic papers related to LLM Security Application. The repository includes papers sorted by conference name and published year, covering topics such as large language models for blockchain security, software engineering, machine learning, and more. Developers and researchers are welcome to contribute additional published papers to the list. The repository also provides information on listed conferences and journals related to security, networking, software engineering, and cryptography. The papers cover a wide range of topics including privacy risks, ethical concerns, vulnerabilities, threat modeling, code analysis, fuzzing, and more.
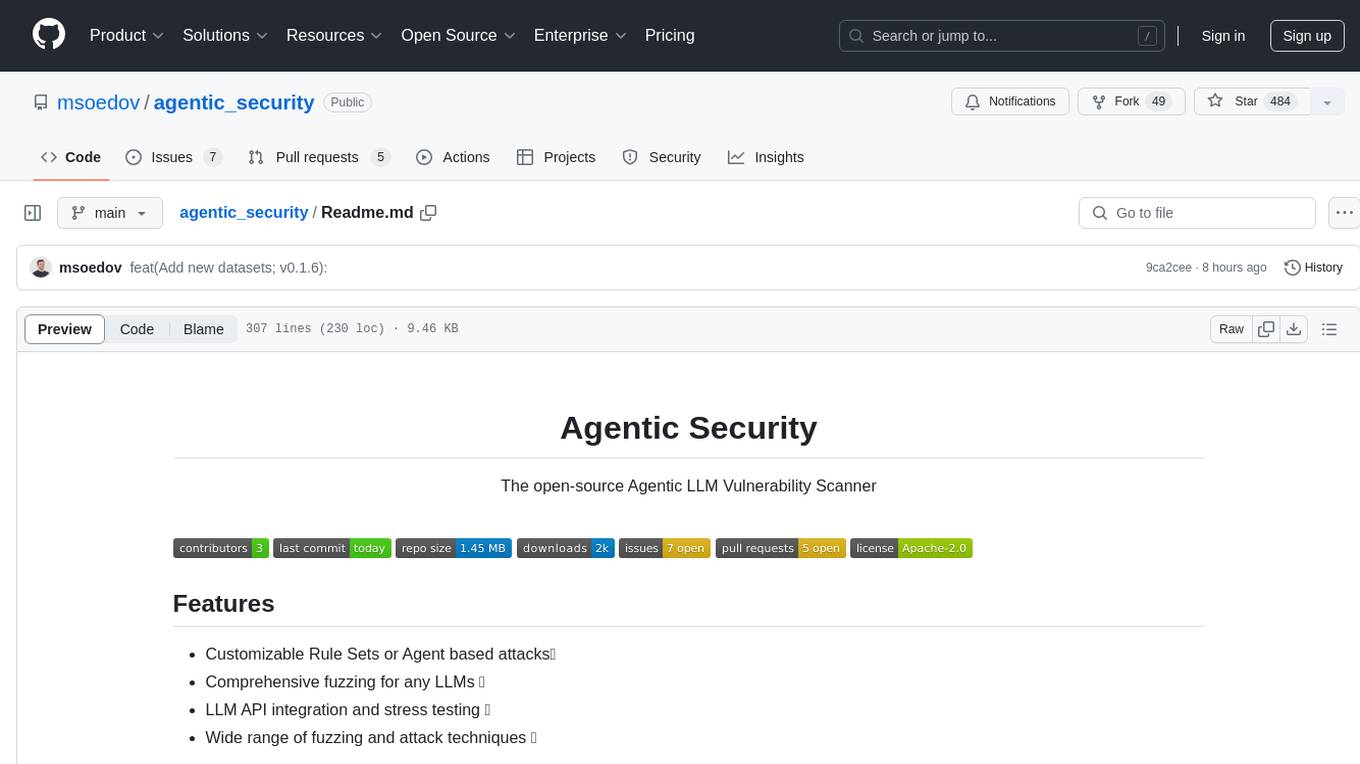
agentic_security
Agentic Security is an open-source vulnerability scanner designed for safety scanning, offering customizable rule sets and agent-based attacks. It provides comprehensive fuzzing for any LLMs, LLM API integration, and stress testing with a wide range of fuzzing and attack techniques. The tool is not a foolproof solution but aims to enhance security measures against potential threats. It offers installation via pip and supports quick start commands for easy setup. Users can utilize the tool for LLM integration, adding custom datasets, running CI checks, extending dataset collections, and dynamic datasets with mutations. The tool also includes a probe endpoint for integration testing. The roadmap includes expanding dataset variety, introducing new attack vectors, developing an attacker LLM, and integrating OWASP Top 10 classification.
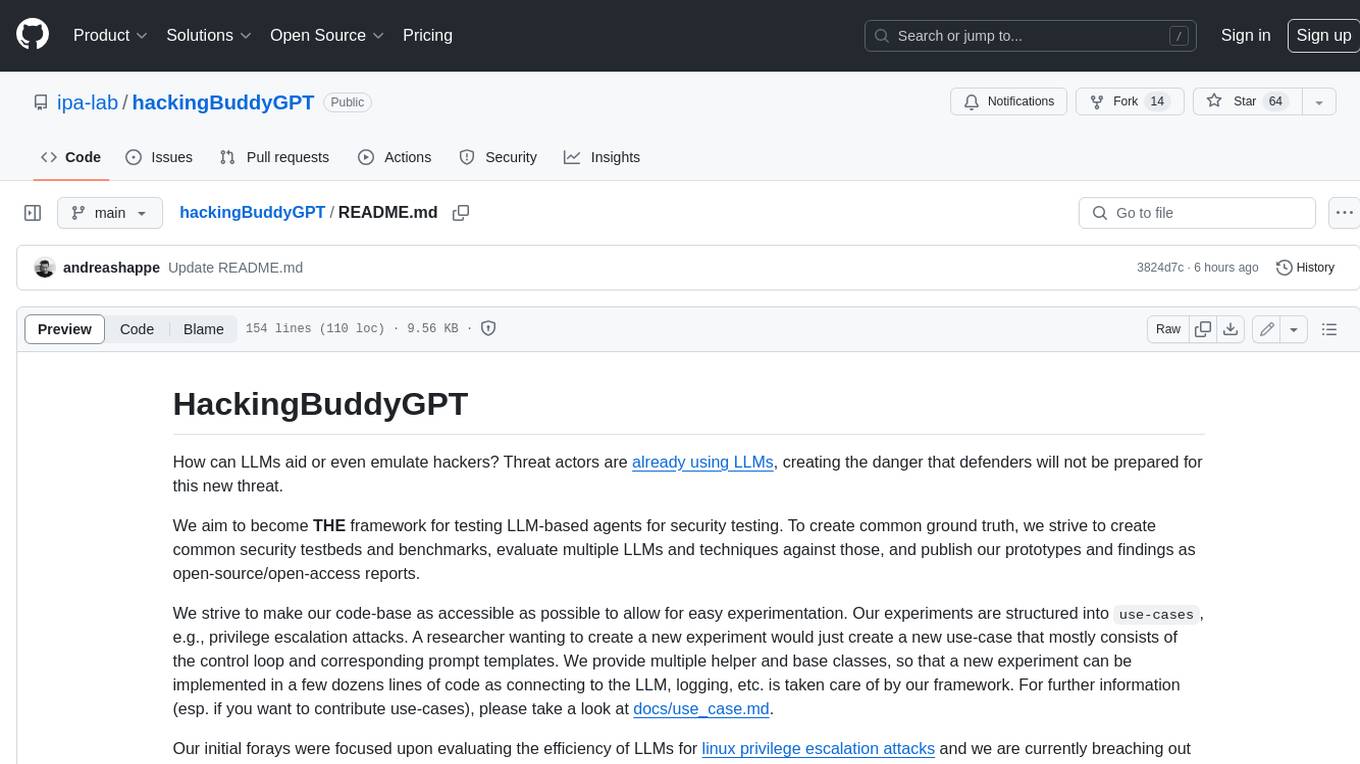
hackingBuddyGPT
hackingBuddyGPT is a framework for testing LLM-based agents for security testing. It aims to create common ground truth by creating common security testbeds and benchmarks, evaluating multiple LLMs and techniques against those, and publishing prototypes and findings as open-source/open-access reports. The initial focus is on evaluating the efficiency of LLMs for Linux privilege escalation attacks, but the framework is being expanded to evaluate the use of LLMs for web penetration-testing and web API testing. hackingBuddyGPT is released as open-source to level the playing field for blue teams against APTs that have access to more sophisticated resources.
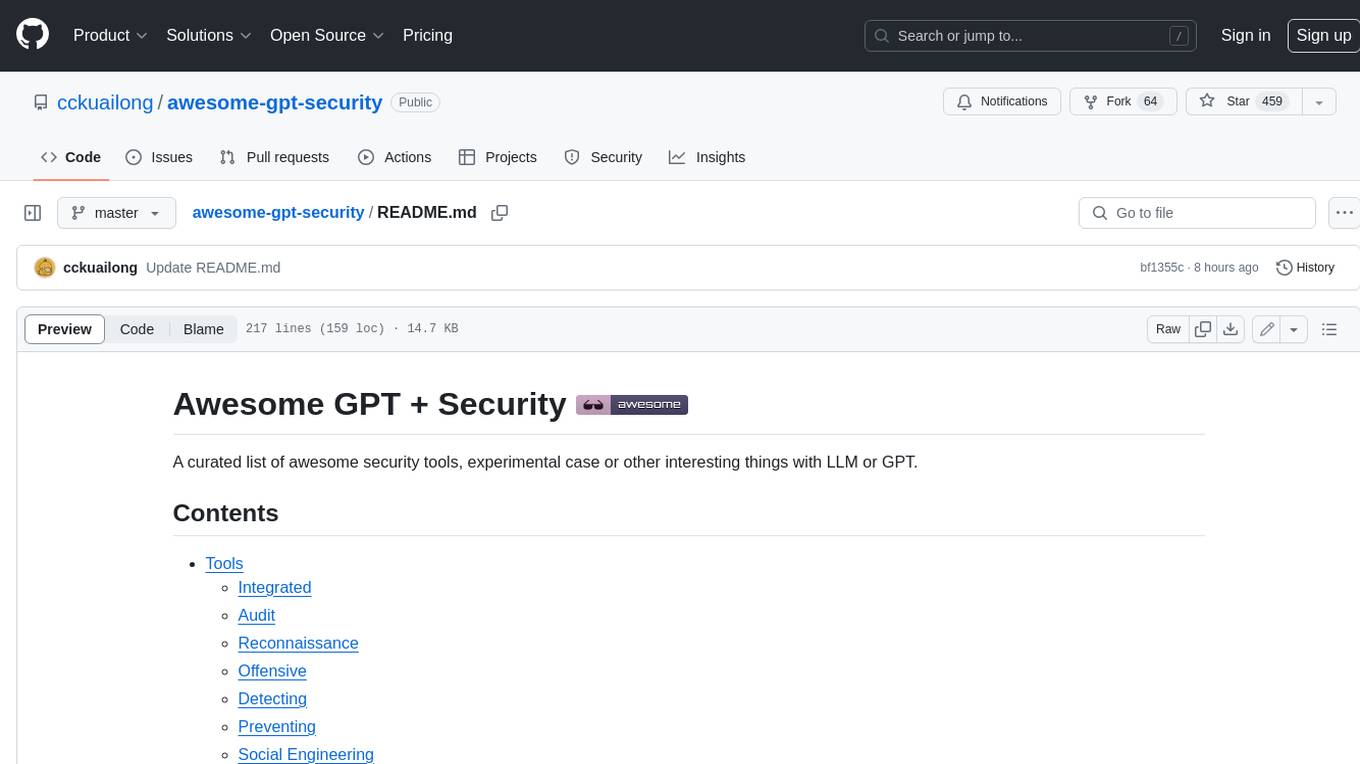
awesome-gpt-security
Awesome GPT + Security is a curated list of awesome security tools, experimental case or other interesting things with LLM or GPT. It includes tools for integrated security, auditing, reconnaissance, offensive security, detecting security issues, preventing security breaches, social engineering, reverse engineering, investigating security incidents, fixing security vulnerabilities, assessing security posture, and more. The list also includes experimental cases, academic research, blogs, and fun projects related to GPT security. Additionally, it provides resources on GPT security standards, bypassing security policies, bug bounty programs, cracking GPT APIs, and plugin security.
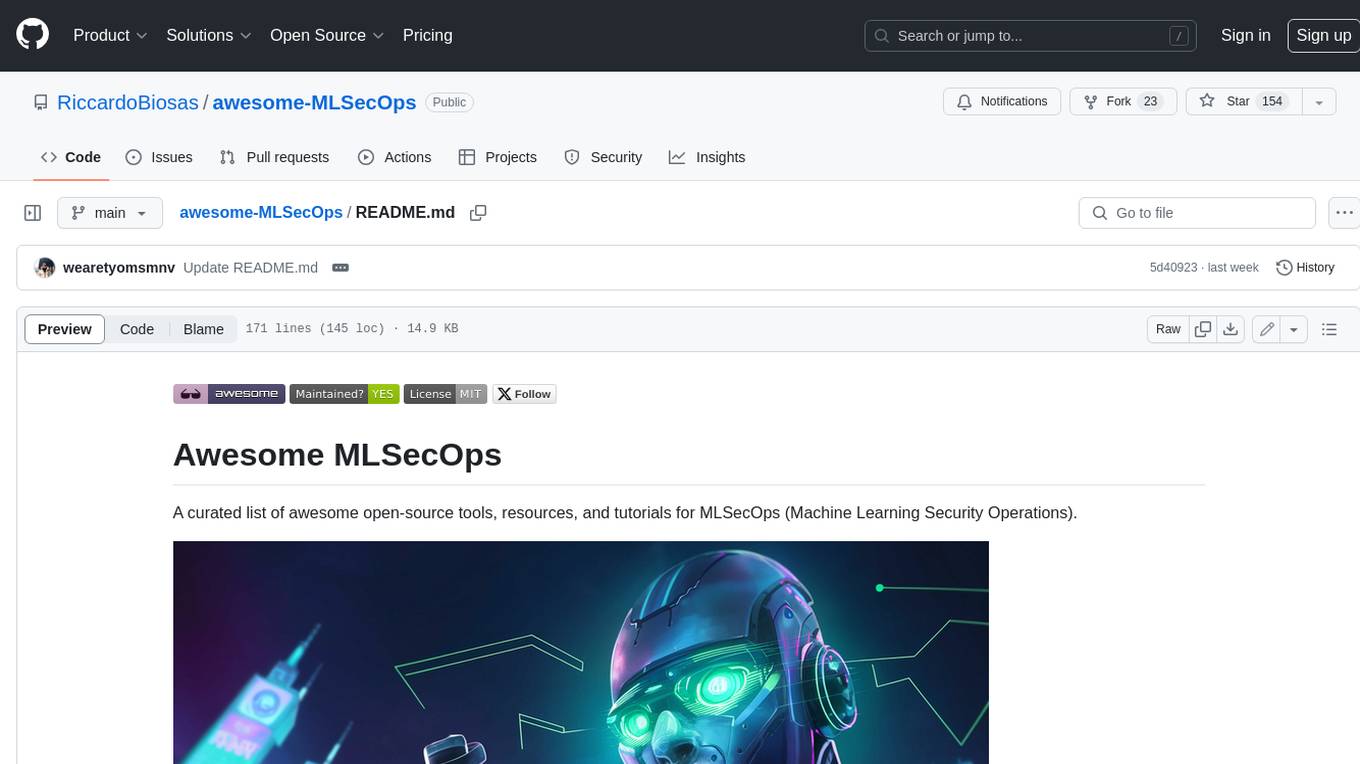
awesome-MLSecOps
Awesome MLSecOps is a curated list of open-source tools, resources, and tutorials for MLSecOps (Machine Learning Security Operations). It includes a wide range of security tools and libraries for protecting machine learning models against adversarial attacks, as well as resources for AI security, data anonymization, model security, and more. The repository aims to provide a comprehensive collection of tools and information to help users secure their machine learning systems and infrastructure.
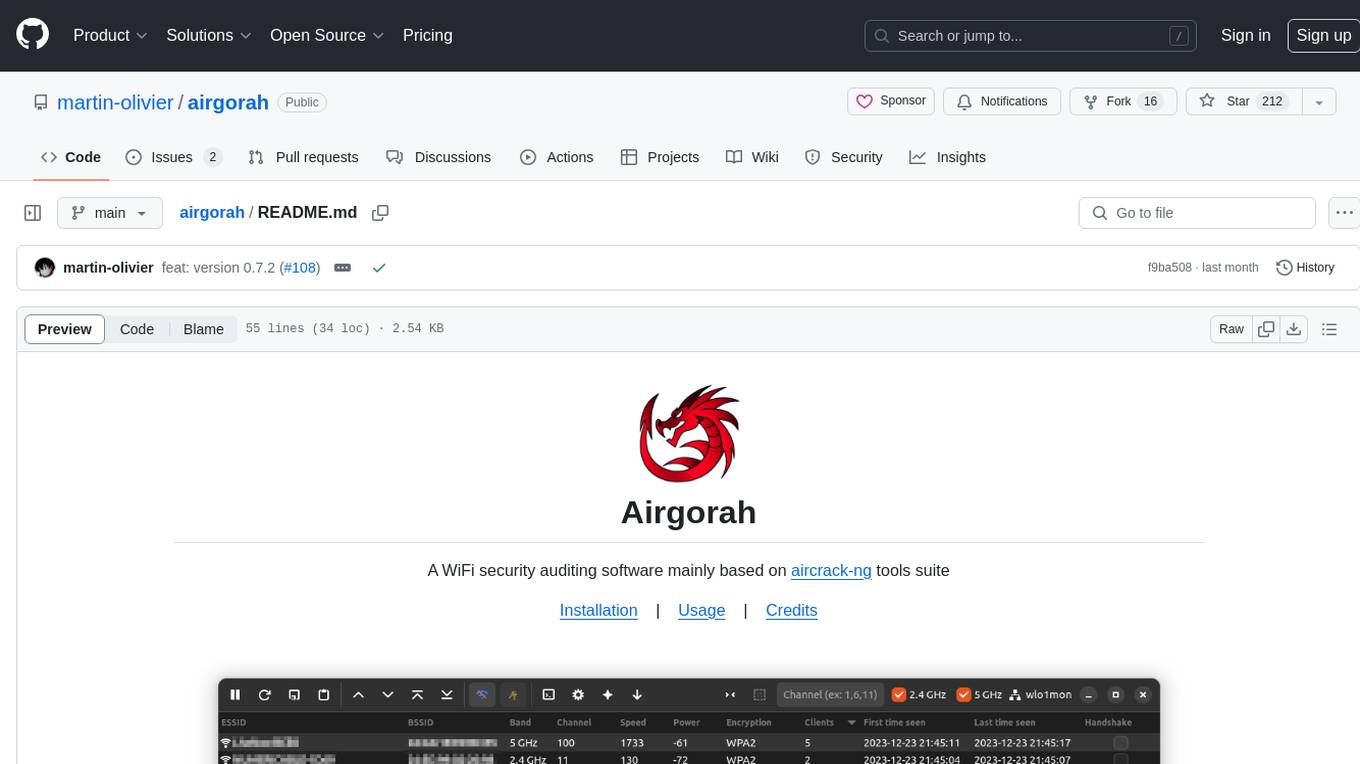
airgorah
Airgorah is a WiFi security auditing software written in Rust that utilizes the aircrack-ng tools suite. It allows users to capture WiFi traffic, discover connected clients, perform deauthentication attacks, capture handshakes, and crack access point passwords. The software is designed for testing and discovering flaws in networks owned by the user, and requires root privileges to run on Linux systems with a wireless network card supporting monitor mode and packet injection. Airgorah is not responsible for any illegal activities conducted with the software.
stride-gpt
STRIDE GPT is an AI-powered threat modelling tool that leverages Large Language Models (LLMs) to generate threat models and attack trees for a given application based on the STRIDE methodology. Users provide application details, such as the application type, authentication methods, and whether the application is internet-facing or processes sensitive data. The model then generates its output based on the provided information. It features a simple and user-friendly interface, supports multi-modal threat modelling, generates attack trees, suggests possible mitigations for identified threats, and does not store application details. STRIDE GPT can be accessed via OpenAI API, Azure OpenAI Service, Google AI API, or Mistral API. It is available as a Docker container image for easy deployment.
Evilginx3-Phishlets
This repository contains custom Evilginx phishlets that are meticulously crafted and updated for real-world applications. It also offers an advanced course, EvilGoPhish Mastery, focusing on phishing and smishing techniques using EvilGoPhish 3.0. The course complements the repository by providing in-depth guidance on deploying these scripts for red team phishing and smishing campaigns.

free-for-life
A massive list including a huge amount of products and services that are completely free! ⭐ Star on GitHub • 🤝 Contribute # Table of Contents * APIs, Data & ML * Artificial Intelligence * BaaS * Code Editors * Code Generation * DNS * Databases * Design & UI * Domains * Email * Font * For Students * Forms * Linux Distributions * Messaging & Streaming * PaaS * Payments & Billing * SSL
chatgpt-universe
ChatGPT is a large language model that can generate human-like text, translate languages, write different kinds of creative content, and answer your questions in a conversational way. It is trained on a massive amount of text data, and it is able to understand and respond to a wide range of natural language prompts. Here are 5 jobs suitable for this tool, in lowercase letters: 1. content writer 2. chatbot assistant 3. language translator 4. creative writer 5. researcher
ai-exploits
AI Exploits is a repository that showcases practical attacks against AI/Machine Learning infrastructure, aiming to raise awareness about vulnerabilities in the AI/ML ecosystem. It contains exploits and scanning templates for responsibly disclosed vulnerabilities affecting machine learning tools, including Metasploit modules, Nuclei templates, and CSRF templates. Users can use the provided Docker image to easily run the modules and templates. The repository also provides guidelines for using Metasploit modules, Nuclei templates, and CSRF templates to exploit vulnerabilities in machine learning tools.
20 - OpenAI Gpts
GetPaths
This GPT takes in content related to an application, such as HTTP traffic, JavaScript files, source code, etc., and outputs lists of URLs that can be used for further testing.
CISSP Study Strategy Guide
Expert guide for CISSP topics, with detailed explanations and real-world application.
Java Security Expert
Java Security Expert offering advice on best practices and resolving security issues.
IoE - Internet of Everything Advisor
Advanced IoE-focused GPT, excelling in domain knowledge, security awareness, and problem-solving, powered by OpenAI
Cloud Computing
Expert in cloud computing, offering insights on services, security, and infrastructure.
Token Securities Insights
A witty, crypto-savvy GPT for token securities insights, balancing humor and professionalism.
Polygon ID Guru
Expert in Polygon ID, aiding in code writing and project building with ZK Proofs.
University Application Guider
Expert in tailored college application and document preparation.