Best AI tools for< Analyze Security Incidents >
20 - AI tool Sites
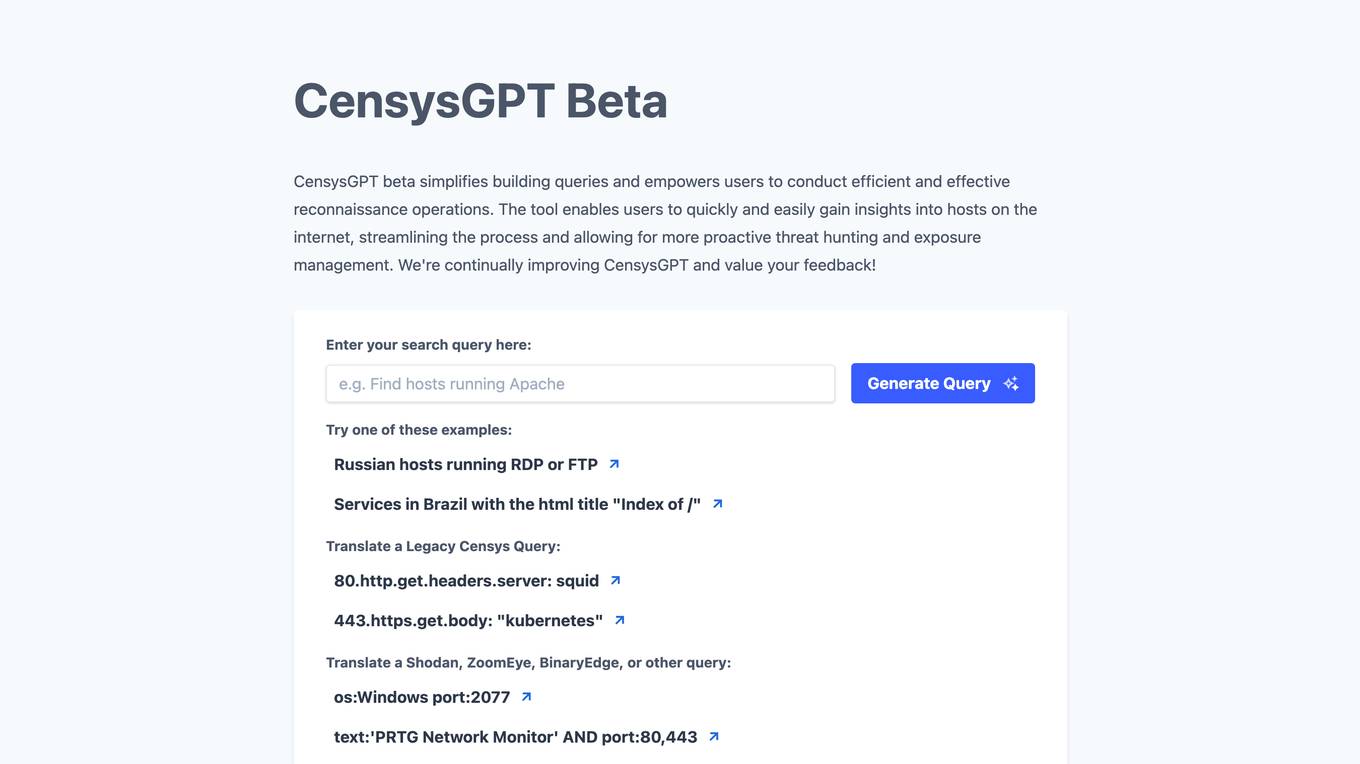
CensysGPT Beta
CensysGPT Beta is a tool that simplifies building queries and empowers users to conduct efficient and effective reconnaissance operations. It enables users to quickly and easily gain insights into hosts on the internet, streamlining the process and allowing for more proactive threat hunting and exposure management.
Ascento
Ascento is an AI-powered security solution that combines robotics and artificial intelligence to secure assets and provide quantitative insights of premises. The application offers features such as detecting people on premises, verifying perimeter integrity, recording property lights, scanning for thermal anomalies, controlling parking lots, and checking doors and windows. Ascento provides advantages like faster threat detection with greater accuracy, cost reduction, autonomous all-terrain robot capabilities, encrypted live communication, and integration with existing video management systems. However, some disadvantages include the need for immediate cost-benefits, training and onboarding requirements, and limited battery life for autonomous charging. The application is suitable for various industries and offers a turnkey solution with 24/7 support and fast replacements.
Resolvd
Resolvd is an AI-powered incident resolution platform that creates a knowledge base of logs, data sources, and applications to autonomously diagnose and resolve incidents. It helps cut time to response by 50%, return hours to developers, simplify data querying, and provide automated anomaly detection. Resolvd uses AI/ML models to analyze logs, aggregate critical context, and deliver insights in workflow, seamlessly integrating with existing systems like Slack, Jira, and PagerDuty.
SentinelOne
SentinelOne is an advanced enterprise cybersecurity AI platform that offers a comprehensive suite of AI-powered security solutions for endpoint, cloud, and identity protection. The platform leverages artificial intelligence to anticipate threats, manage vulnerabilities, and protect resources across the entire enterprise ecosystem. With features such as Singularity XDR, Purple AI, and AI-SIEM, SentinelOne empowers security teams to detect and respond to cyber threats in real-time. The platform is trusted by leading enterprises worldwide and has received industry recognition for its innovative approach to cybersecurity.

Dropzone AI
Dropzone AI is an award-winning AI application designed to reinforce Security Operations Centers (SOCs) by providing autonomous AI analysts. It replicates the techniques of elite analysts to autonomously investigate alerts, covering various use cases such as phishing, endpoint, network, cloud, identity, and insider threats. The application offers pre-trained AI agents that work alongside human analysts, automating investigation tasks and providing fast, detailed, and accurate reports. With built-in integrations with major security tools, Dropzone AI aims to reduce Mean Time to Respond (MTTR) and allow analysts to focus on addressing real threats.
Spot AI
Spot AI is an AI camera system and video surveillance platform that offers AI Security Guard and AI Operations Assistant services. It provides extra protection without the payroll, scales the best operators, and deploys AI agents to standardize operations, coach teams, and execute real-time actions. The platform converts critical moments into context-rich judgments, launches automatic actions, and allows users to analyze, dissect, grade, and relay video content in seconds. Spot AI offers premium cameras, cloud dashboard for incident resolution, and intelligent video recording with on-edge AI processing. It helps enhance safety, efficiency, and productivity across various industries.
Darktrace
Darktrace is an essential AI cybersecurity platform that offers proactive protection, cloud-native AI security, comprehensive risk management, and user protection across various devices. It accelerates triage by 10x, defends with confidence, and connects with various integrations. Darktrace ActiveAI Security Platform spots novel threats across organizations, providing solutions for ransomware, APTs, phishing, data loss, and more. With a focus on defense, Darktrace aims to transform cybersecurity by detecting and responding to known and novel threats in real-time.
MixMode
MixMode is the world's most advanced AI for threat detection, offering a dynamic threat detection platform that utilizes patented Third Wave AI technology. It provides real-time detection of known and novel attacks with high precision, self-supervised learning capabilities, and context-awareness to defend against modern threats. MixMode empowers modern enterprises with unprecedented speed and scale in threat detection, delivering unrivaled capabilities without the need for predefined rules or human input. The platform is trusted by top security teams and offers rapid deployment, customization to individual network dynamics, and state-of-the-art AI-driven threat detection.
Hatchet
Hatchet is an AI companion designed to assist on-call engineers in incident response by providing intelligent insights and suggestions based on logs, communications channels, and code analysis. It helps save time and money by automating the triaging and investigation process during critical incidents. The tool is built by engineers with a focus on data security, offering self-hosted deployments, permissions, audit trails, SSO, and version control. Hatchet aims to streamline incident resolution for tier-1 services, enabling faster response and potential problem resolution.
DataVisor
DataVisor is a modern, end-to-end fraud and risk SaaS platform powered by AI and advanced machine learning for financial institutions and large organizations. It helps businesses combat various fraud and financial crimes in real time. DataVisor's platform provides comprehensive fraud detection and prevention capabilities, including account onboarding, application fraud, ATO prevention, card fraud, check fraud, FinCrime and AML, and ACH and wire fraud detection. The platform is designed to adapt to new fraud incidents immediately with real-time data signal orchestration and end-to-end workflow automation, minimizing fraud losses and maximizing fraud detection coverage.
VOLT AI
VOLT AI is a cloud-based enterprise security application that utilizes advanced AI technology to intercept threats in real-time. The application offers solutions for various industries such as education, corporate, and cities, focusing on perimeter security, medical emergencies, and weapons detection. VOLT AI provides features like unified cameras, video intelligence, real-time notifications, automated escalations, and digital twin creation for advanced situational awareness. The application aims to enhance safety and security by detecting security risks and notifying users promptly.
ODIN
ODIN is a powerful internet scanning search engine designed for scanning and cataloging internet assets. It offers enhanced scanning capabilities, faster refresh rates, and comprehensive visibility into open ports. With over 45 modules covering various aspects like HTTP, Elasticsearch, and Redis, ODIN enriches data and provides accurate and up-to-date information. The application uses AI/ML algorithms to detect exposed buckets, files, and potential vulnerabilities. Users can perform granular searches, access exploit information, and integrate effortlessly with ODIN's API, SDKs, and CLI. ODIN allows users to search for hosts, exposed buckets, exposed files, and subdomains, providing detailed insights and supporting diverse threat intelligence applications.
ODIN
ODIN is a powerful internet scanning search engine designed for scanning and cataloging internet assets. It offers enhanced scanning capabilities, faster refresh rates, and comprehensive visibility into open ports. With over 45 modules covering various services, ODIN provides detailed insights using Lucene query syntax. It identifies potential CVEs, accesses exploit information, and enables reverse searches for threat investigations. ODIN also offers AI/ML-based exposed buckets detection, API integration, and SDKs in multiple languages. Users can search for hosts, exposed buckets, exposed files, and subdomains, with granular searches and seamless integrations. The application is developer-friendly, with APIs, SDKs, and CLI available for automation and programmatic integration.

datasurfr
datasurfr is an AI-driven risk monitoring and analysis platform augmented by human intelligence. It provides operational risk data and intelligence that is curated, customized, and comprehensive. The platform offers tailored alerts detected by AI, curated by surfers, and analyzed by subject matter experts for global security teams. datasurfr also offers predictive risk analytics, proactive alert risk assessment, resilience strategy, data-driven decision-making, supply chain resilience, dynamic incident response, regulatory compliance, and future-proofing strategies. The platform's algorithm works on AI detection and structuring, while human-based smart curation eliminates irrelevant data. Subject matter experts provide event summaries with insights and recommendations. datasurfr offers multi-modal communication through intuitive dashboards, mobile apps, emails, WhatsApp, and seamless APIs for versatile consumption.
CYBER AI
CYBER AI is a security report savant powered by DEPLOYH.AI that simplifies cybersecurity for businesses. It offers a range of features to help organizations understand, unlock, and uncover security threats, including security reports, databreach reports, logs, and threat hunting. With CYBER AI, businesses can gain a comprehensive view of their security posture and take proactive steps to mitigate risks.
Traceable
Traceable is an AI-driven application designed to enhance API security for Cloud-Native Apps. It collects API traffic across the application landscape and utilizes advanced context-based behavioral analytics AI engine to provide insights on APIs, data exposure, threat analytics, and forensics. The platform offers features for API cataloging, activity monitoring, endpoint details, ownership, vulnerabilities, protection against security events, testing, analytics, and more. Traceable also allows for role-based access control, policy configuration, data classification, and integration with third-party solutions for data collection and security. It is a comprehensive tool for API security and threat detection in modern cloud environments.
Sexy.ai
Sexy.ai is an AI-powered security service provided by Cloudflare to protect websites from online attacks. It helps in identifying and blocking malicious activities such as submitting certain words or phrases, SQL commands, or malformed data. The tool uses advanced algorithms to detect potential threats and prevent unauthorized access to websites. Sexy.ai ensures the safety and integrity of online platforms by offering robust security solutions.
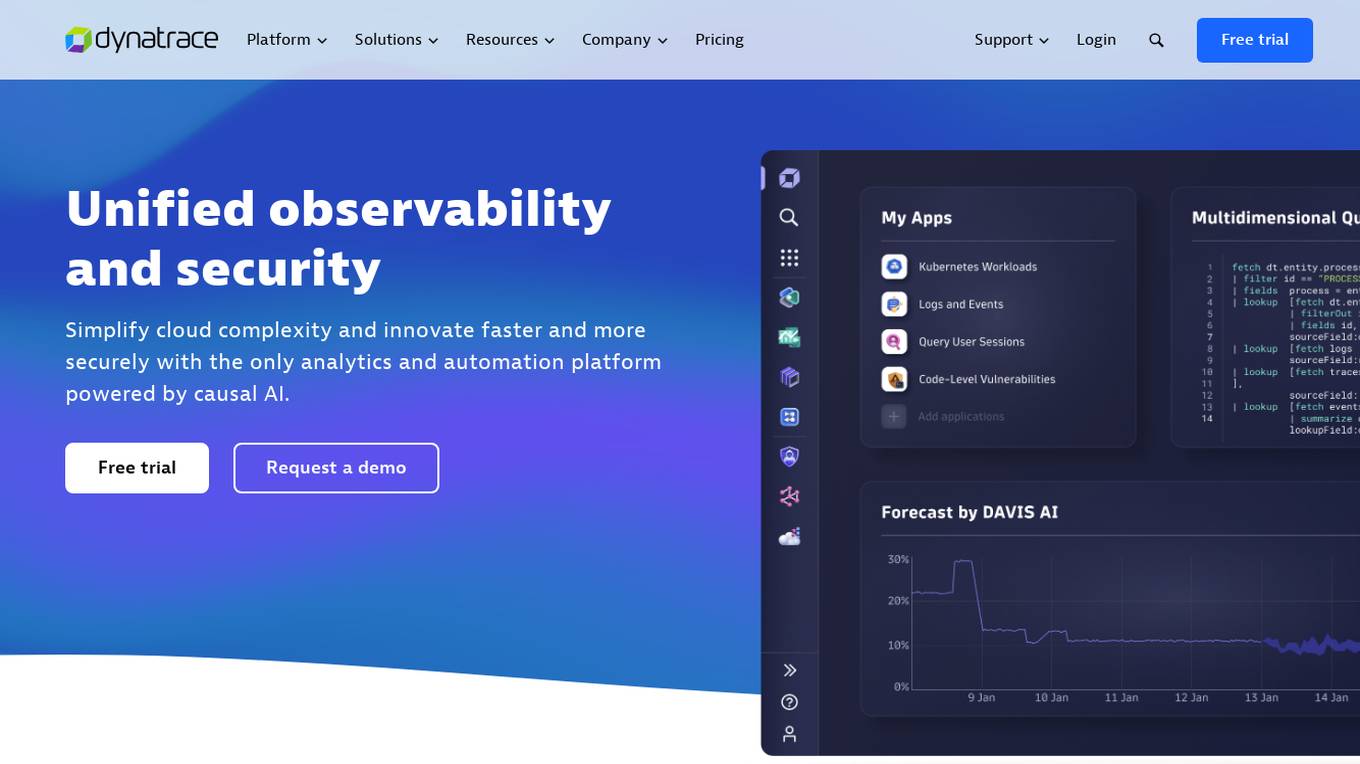
Dynatrace
Dynatrace is a modern cloud platform that offers unified observability and security solutions to simplify cloud complexity and drive innovation. Powered by causal AI, Dynatrace provides analytics and automation capabilities to help businesses monitor and secure their full stack, solve digital challenges, and make better business decisions in real-time. Trusted by thousands of global brands, Dynatrace empowers teams to deliver flawless digital experiences, drive intelligent cloud ecosystem automations, and solve any use-case with custom solutions.
Coalition for Secure AI (CoSAI)
The Coalition for Secure AI (CoSAI) is an open ecosystem of AI and security experts dedicated to sharing best practices for secure AI deployment and collaborating on AI security research and product development. It aims to foster a collaborative ecosystem of diverse stakeholders to invest in AI security research collectively, share security expertise and best practices, and build technical open-source solutions for secure AI development and deployment.
TechSpective
TechSpective is an AI tool that provides technology reviews, podcasts, security insights, and Microsoft news and analysis. The platform offers in-depth articles on cybersecurity, artificial intelligence, and emerging technologies. Users can stay informed about the latest trends in the tech industry and learn about innovative products and solutions.
0 - Open Source AI Tools
20 - OpenAI Gpts
Cyber security analyst
Designed to help cybersecurity analysts # ISO # NIST # COBIT # SANS # PCI DSS
CISO GPT
Specialized LLM in computer security, acting as a CISO with 20 years of experience, providing precise, data-driven technical responses to enhance organizational security.
TheDFIRReport Assistant
Detailed insights from TheDFIRReport's 2021-2023 reports, including Detections and Indicators.
Incident Response Forensic Techniques
help organizations in investigating computer security incidents and troubleshooting some information technology (IT) operational problems by providing practical guidance on performing computer and network forensics.
API Content Warehouse Leak Help
Comprehensive analysis of Google API Content Warehouse Leak
Threat Intelligence Expert
Patient threat intelligence expert skilled in binary file analysis and YARA rules.
ethicallyHackingspace (eHs)® METEOR™ STORM™
Multiple Environment Threat Evaluation of Resources (METEOR)™ Space Threats and Operational Risks to Mission (STORM)™ non-profit product AI co-pilot
MagicUnprotect
This GPT allows to interact with the Unprotect DB to retrieve knowledge about malware evasion techniques
Message Header Analyzer
Analyzes email headers for security insights, presenting data in a structured table view.
Malware Rule Master
Expert in malware analysis and Yara rules, using web sources for specifics.