Best AI tools for< Detect Security Incidents >
20 - AI tool Sites

Cyguru
Cyguru is an all-in-one cloud-based AI Security Operation Center (SOC) that offers a comprehensive range of features for a robust and secure digital landscape. Its Security Operation Center is the cornerstone of its service domain, providing AI-Powered Attack Detection, Continuous Monitoring for Vulnerabilities and Misconfigurations, Compliance Assurance, SecPedia: Your Cybersecurity Knowledge Hub, and Advanced ML & AI Detection. Cyguru's AI-Powered Analyst promptly alerts users to any suspicious behavior or activity that demands attention, ensuring timely delivery of notifications. The platform is accessible to everyone, with up to three free servers and subsequent pricing that is more than 85% below the industry average.
Ambient.ai
Ambient.ai is an AI-powered platform that offers Agentic Physical Security solutions to prevent security incidents. It unifies monitoring, access control, threat assessment, response, and investigations through an always-on reasoning layer. The platform is trusted by leading security teams across various industries such as corporate campuses, education, manufacturing, energy & utilities, healthcare, and financial services. Ambient.ai uses advanced AI monitoring to provide proactive security measures, detect threats, and reduce false alarms. The platform includes features like Foundation for real-time monitoring, Advanced Forensics for quick investigation, Access Intelligence for clearing false alarms, and Threat Detection for incident prevention. Ambient Pulsar, an edge-optimized Vision-Language Model, enhances security operations with reasoning capabilities. The platform is recognized for its leadership in AI for physical security, offering cutting-edge research and perspectives on AI-driven security technologies.
CrowdStrike
CrowdStrike is a cloud-based cybersecurity platform that provides endpoint protection, threat intelligence, and incident response services. It uses artificial intelligence (AI) to detect and prevent cyberattacks. CrowdStrike's platform is designed to be scalable and easy to use, and it can be deployed on-premises or in the cloud. CrowdStrike has a global customer base of over 23,000 organizations, including many Fortune 500 companies.
eightify.app
The website eightify.app is a security service powered by Cloudflare to protect itself from online attacks. It helps in preventing unauthorized access and malicious activities on the website by blocking potential threats. Users may encounter a block if they trigger certain actions like submitting specific words or phrases, SQL commands, or malformed data. In such cases, they can contact the site owner to resolve the issue by providing details of the blocked activity and the Cloudflare Ray ID.
CyberGen
CyberGen is an AI-powered platform that offers advanced security solutions and digital transformation services. It leverages artificial intelligence to provide cutting-edge cybersecurity measures and streamline digital processes for businesses. With a focus on innovation and efficiency, CyberGen helps organizations enhance their security posture and adapt to the evolving digital landscape.
Torq
Torq is an AI-driven platform that offers Security Hyperautomation Solutions, empowering security teams to detect, prioritize, and respond to threats faster. It provides a range of features and capabilities such as AI Agents, AI SOC Analyst, Case Management, and Integrations. Torq is trusted by top security teams worldwide and is recognized for its ability to mitigate alert fatigue, false positives, and staff burnout. The platform is designed to usher in the era of Autonomous SOC by harnessing AI to enhance security operations.
Stellar Cyber
Stellar Cyber is an AI-driven unified security operations platform powered by Open XDR. It offers a single platform with NG-SIEM, NDR, and Open XDR, providing security capabilities to take control of security operations. The platform helps organizations detect, correlate, and respond to threats fast using AI technology. Stellar Cyber is designed to protect the entire attack surface, improve security operations performance, and reduce costs while simplifying security operations.
Exabeam
Exabeam is a cybersecurity and compliance platform that offers Security Information and Event Management (SIEM) solutions. The platform provides flexible choices for threat detection, investigation, and response, whether through cloud-based AI-driven solutions or on-premises SIEM deployments. Exabeam's AI-driven Security Operations Platform combines advanced threat detection capabilities with automation to deliver faster and more accurate TDIR. With features like UEBA, SOAR, and insider threat detection, Exabeam helps organizations improve security posture and optimize investments. The platform supports various industries and use cases, offering pre-built content, behavioral analytics, and context enrichment for enhanced threat coverage and compliance.
Ascento
Ascento is an AI-powered security solution that combines robotics and artificial intelligence to secure assets and provide quantitative insights of premises. The application offers features such as detecting people on premises, verifying perimeter integrity, recording property lights, scanning for thermal anomalies, controlling parking lots, and checking doors and windows. Ascento provides advantages like faster threat detection with greater accuracy, cost reduction, autonomous all-terrain robot capabilities, encrypted live communication, and integration with existing video management systems. However, some disadvantages include the need for immediate cost-benefits, training and onboarding requirements, and limited battery life for autonomous charging. The application is suitable for various industries and offers a turnkey solution with 24/7 support and fast replacements.
SentinelOne
SentinelOne is an advanced enterprise cybersecurity AI platform that offers a comprehensive suite of AI-powered security solutions for endpoint, cloud, and identity protection. The platform leverages artificial intelligence to anticipate threats, manage vulnerabilities, and protect resources across the entire enterprise ecosystem. With features such as Singularity XDR, Purple AI, and AI-SIEM, SentinelOne empowers security teams to detect and respond to cyber threats in real-time. The platform is trusted by leading enterprises worldwide and has received industry recognition for its innovative approach to cybersecurity.
VOLT AI
VOLT AI is a cloud-based enterprise security application that utilizes advanced AI technology to intercept threats in real-time. The application offers solutions for various industries such as education, corporate, and cities, focusing on perimeter security, medical emergencies, and weapons detection. VOLT AI provides features like unified cameras, video intelligence, real-time notifications, automated escalations, and digital twin creation for advanced situational awareness. The application aims to enhance safety and security by detecting security risks and notifying users promptly.
Vectra AI
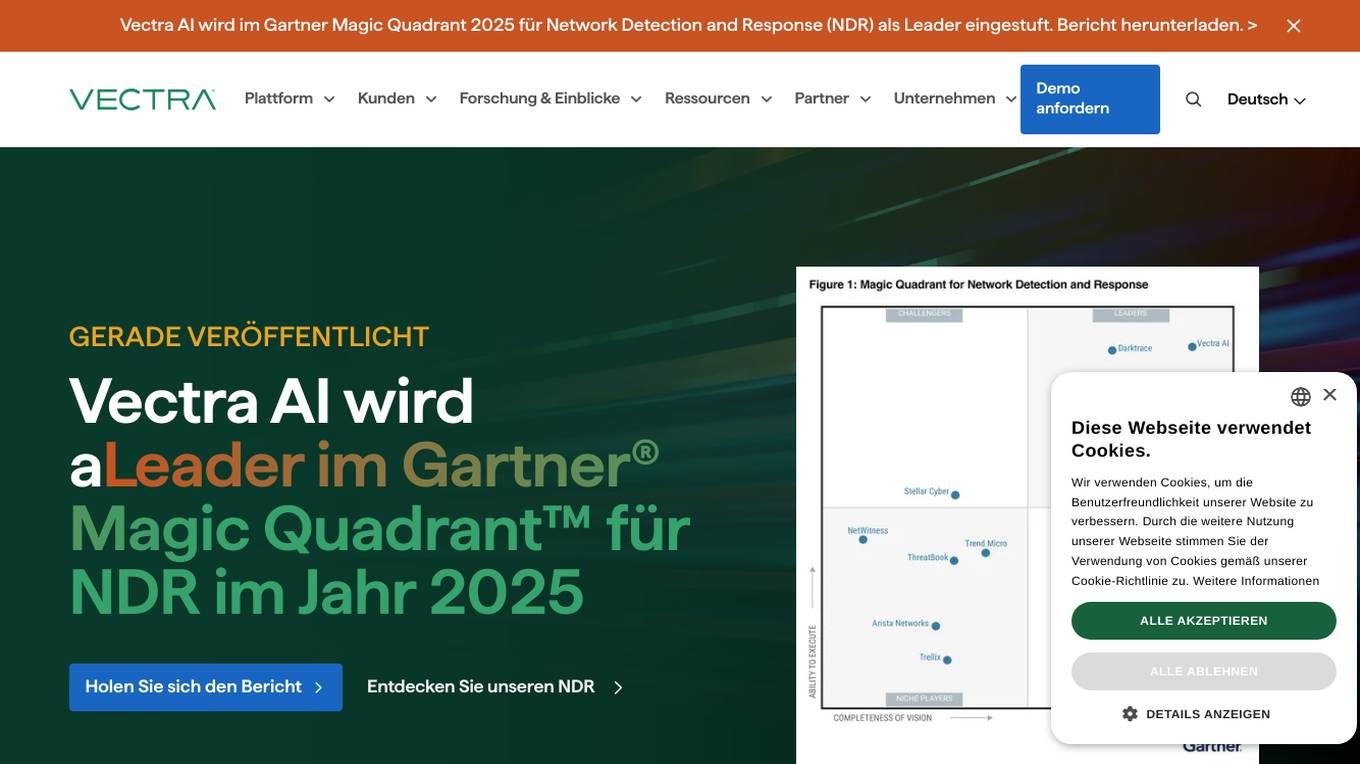
Vectra AI is a leading AI security platform that helps organizations stop advanced cyber attacks by providing an integrated signal for extended detection and response (XDR). The platform arms security analysts with real-time intelligence to detect, prioritize, investigate, and respond to threats across network, identity, cloud, and managed services. Vectra AI's AI-driven detections and Attack Signal Intelligence enable organizations to protect against various attack types and emerging threats, enhancing cyber resilience and reducing risks in critical infrastructure, cloud environments, and remote workforce scenarios. Trusted by over 1100 enterprises worldwide, Vectra AI is recognized for its expertise in AI security and its ability to stop sophisticated attacks that other technologies may miss.
Darktrace
Darktrace is an essential AI cybersecurity platform that offers proactive protection, cloud-native AI security, comprehensive risk management, and user protection across various devices. It accelerates triage by 10x, defends with confidence, and connects with various integrations. Darktrace ActiveAI Security Platform spots novel threats across organizations, providing solutions for ransomware, APTs, phishing, data loss, and more. With a focus on defense, Darktrace aims to transform cybersecurity by detecting and responding to known and novel threats in real-time.
MixMode
MixMode is the world's most advanced AI for threat detection, offering a dynamic threat detection platform that utilizes patented Third Wave AI technology. It provides real-time detection of known and novel attacks with high precision, self-supervised learning capabilities, and context-awareness to defend against modern threats. MixMode empowers modern enterprises with unprecedented speed and scale in threat detection, delivering unrivaled capabilities without the need for predefined rules or human input. The platform is trusted by top security teams and offers rapid deployment, customization to individual network dynamics, and state-of-the-art AI-driven threat detection.
Vectra AI
Vectra AI is an advanced AI-driven cybersecurity platform that helps organizations detect, prioritize, investigate, and respond to sophisticated cyber threats in real-time. The platform provides Attack Signal Intelligence to arm security analysts with the necessary intel to stop attacks fast. Vectra AI offers integrated signal for extended detection and response (XDR) across various domains such as network, identity, cloud, and endpoint security. Trusted by 1,500 enterprises worldwide, Vectra AI is known for its patented AI security solutions that deliver the best attack signal intelligence on the planet.
DataVisor
DataVisor is a modern, end-to-end fraud and risk SaaS platform powered by AI and advanced machine learning for financial institutions and large organizations. It helps businesses combat various fraud and financial crimes in real time. DataVisor's platform provides comprehensive fraud detection and prevention capabilities, including account onboarding, application fraud, ATO prevention, card fraud, check fraud, FinCrime and AML, and ACH and wire fraud detection. The platform is designed to adapt to new fraud incidents immediately with real-time data signal orchestration and end-to-end workflow automation, minimizing fraud losses and maximizing fraud detection coverage.
OpenBuckets
OpenBuckets is a web application designed to help users find and secure open buckets in cloud storage systems. It provides a user-friendly interface for scanning and identifying unprotected buckets, allowing users to take necessary actions to secure their data. With OpenBuckets, users can easily detect potential security risks and prevent unauthorized access to their sensitive information stored in the cloud.
Palo Alto Networks
Palo Alto Networks is a cybersecurity company offering advanced security solutions powered by Precision AI to protect modern enterprises from cyber threats. The company provides network security, cloud security, and AI-driven security operations to defend against AI-generated threats in real time. Palo Alto Networks aims to simplify security and achieve better security outcomes through platformization, intelligence-driven expertise, and proactive monitoring of sophisticated threats.
CrowdStrike
CrowdStrike is a leading cybersecurity platform that uses artificial intelligence (AI) to protect businesses from cyber threats. The platform provides a unified approach to security, combining endpoint security, identity protection, cloud security, and threat intelligence into a single solution. CrowdStrike's AI-powered technology enables it to detect and respond to threats in real-time, providing businesses with the protection they need to stay secure in the face of evolving threats.
Vectra AI
Vectra AI is a leading cybersecurity AI application that stops attacks that others cannot. It is recognized in the Gartner Magic Quadrant 2025 for Network Detection and Response (NDR) as a leader. Vectra AI's platform protects modern networks from advanced threats by providing real-time attack signal intelligence and AI-driven detections. It equips security analysts with the information needed to quickly stop attacks across various security application scenarios. The application covers a wide range of security areas such as SOC modernization, SIEM optimization, IDS replacement, EDR extension, cloud resilience, and more.
0 - Open Source AI Tools
20 - OpenAI Gpts
Mónica
CSIRT que lidera un equipo especializado en detectar y responder a incidentes de seguridad, maneja la contención y recuperación, organiza entrenamientos y simulacros, elabora reportes para optimizar estrategias de seguridad y coordina con entidades legales cuando es necesario
CISO GPT
Specialized LLM in computer security, acting as a CISO with 20 years of experience, providing precise, data-driven technical responses to enhance organizational security.
Threat Intelligence Expert
Patient threat intelligence expert skilled in binary file analysis and YARA rules.
Defender for Endpoint Guardian
To assist individuals seeking to learn about or work with Microsoft's Defender for Endpoint. I provide detailed explanations, step-by-step guides, troubleshooting advice, cybersecurity best practices, and demonstrations, all specifically tailored to Microsoft Defender for Endpoint.
Blue Team Guide
it is a meticulously crafted arsenal of knowledge, insights, and guidelines that is shaped to empower organizations in crafting, enhancing, and refining their cybersecurity defenses
ethicallyHackingspace (eHs)® METEOR™ STORM™
Multiple Environment Threat Evaluation of Resources (METEOR)™ Space Threats and Operational Risks to Mission (STORM)™ non-profit product AI co-pilot
MITREGPT
Feed me any input and i'll match it with the relevant MITRE ATT&CK techniques and tactics (@mthcht)
MagicUnprotect
This GPT allows to interact with the Unprotect DB to retrieve knowledge about malware evasion techniques
Malware Rule Master
Expert in malware analysis and Yara rules, using web sources for specifics.
Log Analyzer
I'm designed to help You analyze any logs like Linux system logs, Windows logs, any security logs, access logs, error logs, etc. Please do not share information that You would like to keep private. The author does not collect or process any personal data.